What DNS data says about IoT devices in your home
What are all those IoT devices in your home actually doing on your home network? We ran a little test to find out, and found some interesting info.
Key Takeaways
The number of connected devices per person nearly doubled over the last five years. Every person on earth is now outnumbered by an estimated 6.58 devices.
Ever wonder what all those connected thermostats, TVs, refrigerators, and virtual assistants are actually doing on your home network?
We decided to run a little test and find out.
The test
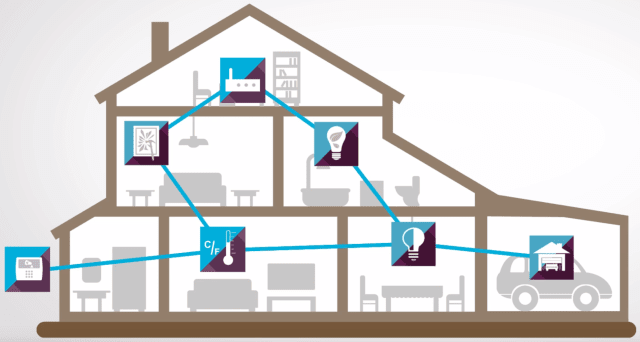
Using BlueCat’s DNS Edge security platform, one of our engineers set up a service point on his home network. Once this service point became the “first hop” of any DNS query, it was able to capture comprehensive logs for all internal and external traffic on the network.
We took logs of three connected devices – a Samsung Smart TV, a Google Home virtual assistant, and a Pioneer receiver – from a 24 hour period. Then we analyzed the traffic to find out exactly what all of these devices and their associated apps were up to.
The results
Home network devices are very predictable. We found that for the most part, connected devices only query a handful of domains. It appears that most of those queries are pings for new updates or firmware downloads. There are a few cloud-based services like Plex (a media application service) which merit a query now and then. But overall, the devices were mostly reaching out to the exact domains you’d expect.
The DNS query success rate is extremely high… We found that 100% of the DNS queries from the TV and the Google Home device resolved as expected. This high success rate, when combined with the predictable usage patterns, make it very easy to spot a compromised device. If we were seeing any domains aside from the usual suspects, it would have been cause for concern. Thankfully, we didn’t.
…Except when it purposely isn’t. Unlike the other devices we tested, around 16% of the DNS queries from the Pioneer receiver returned an NXDOMAIN response. Digging into the data, we discovered that this was on purpose. Every ten minutes, the device would attempt to connect with channel.status.request.url – a non-existent domain. If that ever resolved, it would be an indicator of DNS hijacking. This is a common security measure for apps like Google Chrome. It was interesting to see this kind of protection used in a device as well.
Netflix is extremely chatty. Netflix accounted for a significant number of DNS queries on the connected TV. It was constantly polling content delivery network servers, balancing downloads against different sources to ensure maximum uptime of streamed content. With all these queries, it’s no wonder that Netflix accounts for around fifteen percent of global internet traffic.
Google never stops talking. Netflix queries dropped to zero at night, when the smart TV wasn’t on. The Google Home device, however, sends DNS queries 24/7/365. Almost all of those queries (around 95%) were to various Google services. The remainder were from various sites used to gather information for recipes, trivia answers, Spotify, etc.
What we learned
In the end, the data show that devices on a home network behave a lot like devices on a corporate network. If you compared the information we collected from a typical home-based IoT device against data from over five billion DNS queries on BlueCat-managed corporate networks, the modus operandi of most single-use devices would be very similar.
The predictability of DNS traffic from IoT devices shows just how valuable DNS security can be in detecting and mitigating a breach. If the smart TV suddenly queries a domain outside of the standard handful of usual suspects, you should unplug it immediately. If your Pioneer receiver starts resolving 100% of its queries – including those against the deliberately false one – you have a security problem.
Visibility into those malicious DNS queries is only half the equation. You have to be able to act on threat information quickly. If a service point is there on the first hop of an IoT device’s DNS query, you have the power to stop it. That’s exactly what BlueCat does with its DNS security platform, DNS Edge – it applies security policies to every query, blocking or redirecting queries which sit outside the realm of normal patterns.
Want to learn more? Here’s a quick primer on how BlueCat’s service points make us different.





