- Solutions
- Security
Stronger, faster security built on integrated network intelligence
Combine DNS-layer control with packet-level visibility and real-time flow monitoring to detect threats earlier, respond faster, and enforce policies across your entire network.

Defrag your security infrastructure
Modern enterprise networks are fragmented—spanning cloud, data centers, SD-WAN, and remote users.
A larger and less visible perimeter means attackers have more blind spots to exploit—such as DNS, east-west traffic, and misconfigured infrastructure.
Most security tools only provide glimpses of the full picture. BlueCat’s Protective DNS solutions provide security and network teams with a shared foundation of visibility and control to detect threats early, block malicious traffic, and accelerate response times.
We embed protection and visibility into DNS resolution itself, so your existing infrastructure becomes a proactive layer of defense against malicious attacks and risk.
The BlueCat security suite
BlueCat’s security solutions equip SecOps teams with two layers of visibility and control to secure infrastructure and devices: DNS-layer enforcement throughout core services combined with security observability powered by real-time flow monitoring and packet-level forensics.
This combination means you get a complete and real-time picture of security across the whole network—from the moment a device issues a DNS request to its journey through your environment.
The result is that SecOps teams can detect threats sooner, understand their root causes, and take fast and assured mitigation actions. Use BlueCat’s security solutions to:
Block threats at the first query with DNS-layer controls
Monitor traffic patterns to detect suspicious behavior and lateral movement
Investigate incidents with flow visualization and packet payload inspection
Validate the health and security posture of firewalls, SD-WAN, and cloud infrastructure
Feed high-quality, contextual data into SIEM, SOAR, and analytics tools
DNS-layer security solutions
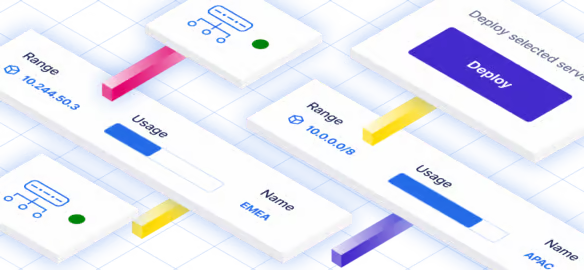
Edge is our intelligent DNS resolver. It’s a caching and recursion layer that works with Integrity and Micetro—our products for managing DNS, DHCP, and IP address management (together known as DDI)—to handle outbound requests to the internet and block malicious DNS queries before they resolve.
Tame complexity
Monitor and analyze every query and IP address to get full context—from one place and across any data center or cloud.
Drive performance
Reduce congestion and improve reliability with multiple optimized resolution paths and fewer overlapping zones.
Stop threats
Detect and stop external threats like tunneling, distributed denial-of-service (DDoS) attacks, beaconing, domain generation algorithms, lateral attacks, data exfiltration—and even malware.
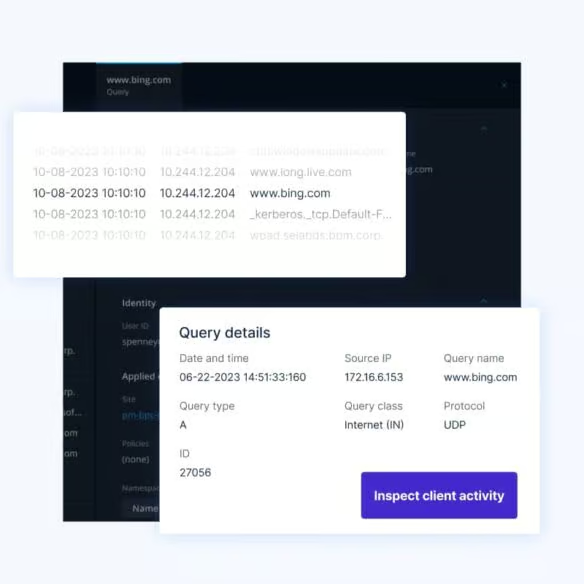
Enhance investigations
Edge gives you better forensics with query logs and user change tracking.
Prevent downtime
Create DNS redundancy for any environment. Centralize all DNS resolution under Edge, or failover to it from cloud-native DNS resolution.
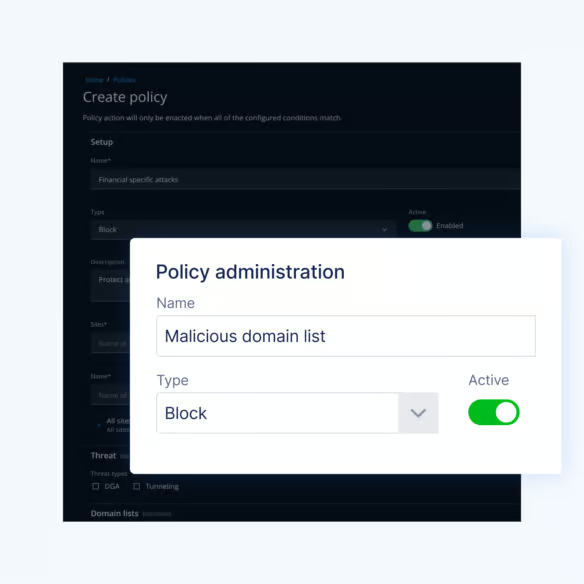
BlueCat’s Threat Protection protects your network from cyber threats by preventing network devices from querying malicious content.
It’s like a DNS firewall that integrates DNS data with the latest threat intelligence from sources such as Crowdstrike. Your security teams can enforce policies that block threat sources from accessing your critical apps and data.

Security observability solutions
LiveNX
LiveNX
Real-time visualization, topology-based flow analysis, and performance metrics to monitor and troubleshoot complex, multi-vendor environments.
LiveWire
LiveWire
High-speed packet capture and deep forensic analysis for root cause investigation, security response, and historical visibility.
LiveSP
LiveSP
Multi-tenant platform for managed service providers and carriers to deliver SLA-driven performance monitoring and reporting to their customers.

Security isn’t separate from operations anymore.
BlueCat’s security solutions help NetOps and SecOps teams work from a shared foundation of real-time network data that connects visibility, control, and response.
This combined approach enables multi-layered threat detection and prevention by integrating DNS-layer security with traffic-level visibility and policy and configuration controls.
The result is an intelligent approach to NetOps that breaks up traditional security silos and coordinates network security across multiple teams and disciplines.
Talk with an expert
Speak with us about DNS-layer security and control for threat detection and policy enforcement.
Related solutions

Network observability and intelligence
Optimize your network and device performance, security, and uptime with solutions that proactively detect issues and offer actionable insight.

Unified DDI
Unify DNS, DHCP, and IPAM with DDI solutions to consolidate, automate, and streamline your core network services on premises or in any cloud.

Network automation
Streamline operations across on-prem, hybrid and multi-cloud networks. BlueCat helps teams automate DDI tasks, unify visibility, and accelerate network…

Multicloud management
Simplify and automate multicloud management with unified DNS visibility across data centers, branches, and public and private cloud networks.
Next Steps
Ready to dive deeper? Explore our technical resources.
Let’s talk about how our solutions can accelerate your network.