Why the Cyber Threat Hunter Needs DNS
In our latest webinar in our cyber security series, we welcome Cyxtera Cyber Security Officer Chris Day.

Key Takeaways
In our latest webinar in our cyber security series, we welcome Cyxtera Cyber Security Officer Chris Day. Our last webinar, former Homeland Security advisor Dick Clarke focused on the changing role of the CISO. This time, Chris Day tackles the issues facing those on the front lines, those who are securing the networks and investigating the breaches: the threat hunters.
Before becoming the Chief Cyber Security Officer at Cyxtera, Chris was also the CISO at Invincea, the CTO for Packet Forensics and Chief Security Architect for Terramark (which was acquired by Verizon). He’s also served on the President’s Secure Government Communications Subcommittee.
Threat hunters are a proactive bunch. Their aim is to act before the damage is done. As Chris puts it, “Cyber threat hunting is about taking that less structured look at your network.” It’s about leveraging tools and data sources that aren’t typically part of your cyber security stack but can still help the hunter glean what has happened during a breach. DNS is traditionally thought of as infrastructure, but by shifting their perspective and changing how they look at DNS data, threat hunters can use DNS as a sensor for network activity. That being said, their biggest challenge isn’t necessarily the data itself, but reading and combing through it.
Chris walks us through the growing role of the threat hunter and how threat hunters can be (and should be) leveraging DNS as a weapon, shining a great deal of light on a few invaluable facets of the threat hunter’s role: the value of DNS data, the humanity behind it, and the insights within it.
Finding the Needle in your DNS Haystack
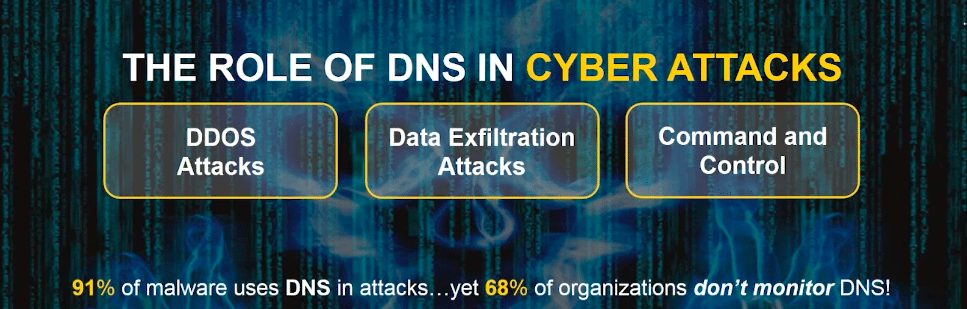
It’s a stat that you may have seen us using repeatedly, mostly because it’s so drastic. 91% of malware uses DNS, and it’s no wonder. “DNS is the central mechanism to connect devices to a network,” emphasizes Chris. It’s also important to control how DNS resolution occurs in your specific network environment. So how can a threat hunter use DNS data to effectively interpret what kind of attack is taking place or has taken place?
Simply, by looking for abnormalities within the DNS data that hint at malicious activity. There are also patterns in the strings themselves. The character count, the frequency of the queries, the age of the domain itself, first-time domain queries – all of these can be indicators of malicious activity.
The Face of Malware is Human
Chris raised an oft-forgotten point: that there is a human being behind all malware. While threat hunters and network engineers are working on the ground within digital environments, there is always a human at work on the other side. And with that humanity comes curiosity, creativity, and unpredictability. Human beings are anything but rational, but that doesn’t mean that they don’t leave behind hints and trails. Finding the right patterns within queries and suspicious-looking domains is where threat hunters earn their title. Because the biggest challenge is not the data itself. It’s finding insights within the data.
Reading Between the Queries
Chris uses tunneling as a prime example pattern-finding. Tunneling moves private data across a network in a way that makes them appear as public. “It opened people’s eyes about how malleable DNS can be and how it can be abused.”
Essentially, tunneling will make a number of rapid, lengthy queries, using the largest number of characters allowed by the DNS RFC’s (Request for Comments).
In order to effectively interpret all this data, Chris prefers “sensors to be as close to the local resolver as possible.” This allows the threat hunter to see every result and query that’s going out even if it’s cached. While this may seem like a lot, there is value in volume. If the local resolver caches a query, but 15 other machines made queries to a domain you’ve never seen before, that’s something worth looking into.
What’s Next for the Threat Hunter?
2017 was defined by large scale cyber attacks like WannaCry and the Mirai botnet. These breaches seriously affected healthcare, financial institutions and more, and Chris believes 2018 will bring more of the same.
“As computers systems are starting to interact more in the physical space, particularly in the IoT space, cyber attacks start to have real-world impact.”
So where does this leave the threat hunter? Well, let’s just say they won’t be out of a job anytime soon. With the rising frequency and complexity of malware attacks, threat hunters and DNS data are more important to cyber security teams than ever.
While there is a “lack of awareness of the security utility” of DNS data, threat hunters can gain invaluable insights from it, even if they’re just analyzing a small amount of data in the queries in CSV files. By focusing on the queries as well as the responses while applying good analytics and heuristics, to use Chris’ terms, the threat hunter will put themselves in a much better position to succeed.





