Temporary workaround for SAD DNS
Ahead of Linux’s patch taking effect, BlueCat Labs has a temporary workaround for protecting against the revived Kaminsky DNS cache poisoning attack.
Key Takeaways
Recently, researchers identified a new way to carry out the Kaminsky DNS cache poisoning attack. Its name is SAD DNS, short for Side-channel AttackeD DNS.
Linux developers have made a change to block this. But it was only introduced into the kernel on October 16, 2020. It may be a while before the change is adopted across most systems, David Maxwell, BlueCat’s Software Security Director, told BleepingComputer.
For BlueCat customers: The customer care portal contains a KI article (KI-024626) that BlueCat is keeping up to date. BlueCat is continually assessing the risk to you and your BlueCat products and suggested steps to take.
For the rest of the community running public BIND-based DNS servers: There is a viable workaround. Linux’s change, once implemented, will randomize ICMP rate limits to stop an attacker from abusing the static rate value to identify a port number. You can achieve a similar outcome with a small shell script.
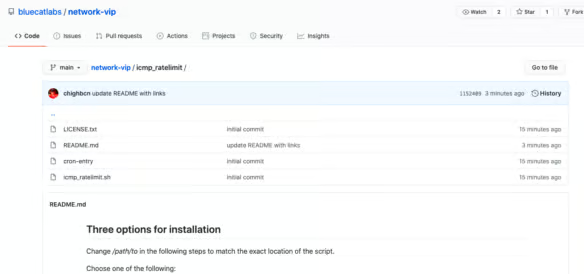
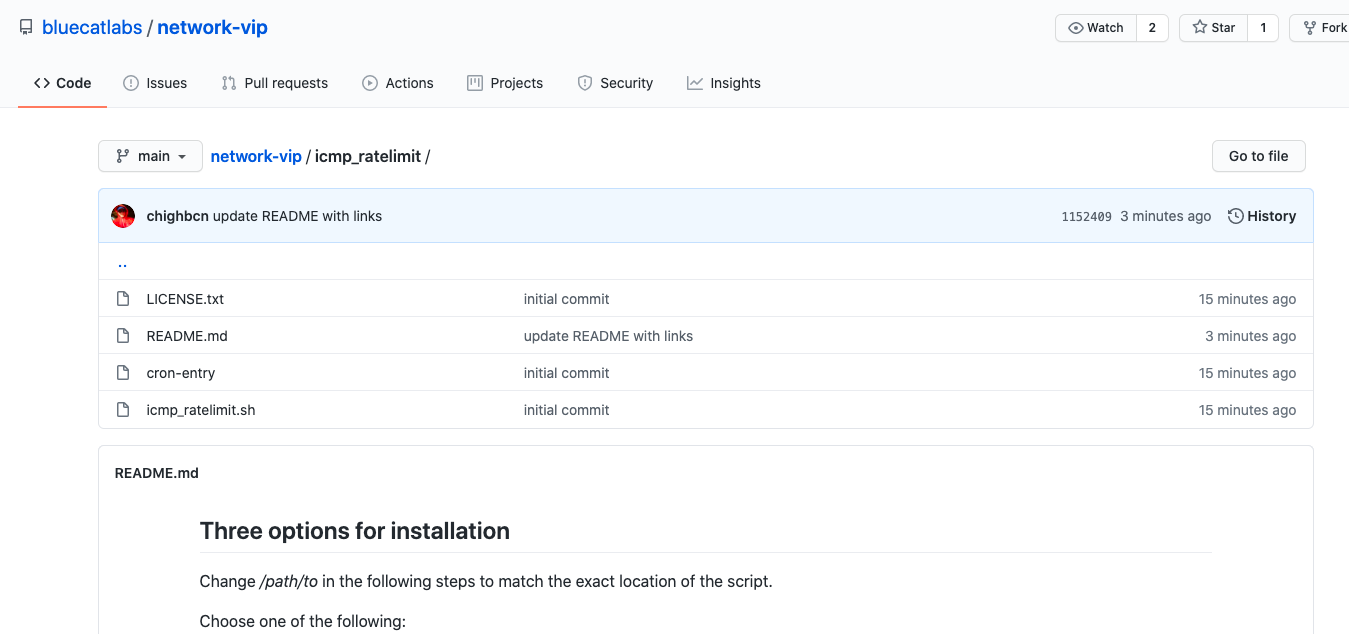
BlueCat’s GitHub repository, BlueCat Labs, now contains the script that members of the broader community can use to randomize ICMP rate limits and reduce risk against SAD DNS.
In addition, BlueCat recommends implementing DNSSEC. BlueCat has also noticed some advice on the internet suggesting to block ICMP altogether; BlueCat recommends against this.




