Is an IP address PII? The answer is nuanced
‘Is an IP address PII’ is a question with real implications for network admins. Explore how countries approach it and what companies should do about it.

Key Takeaways
Is an IP address PII?
For network administrators who deal in thousands of internet protocol addresses daily, the question has real implications. Does an internet protocol (IP) address constitute personal data that can be used to identify a specific individual? And, as such, do organizations have to protect it?
The legal boundaries and technical requirements involved in safeguarding personally identifiable information (PII) are relatively clear. As part of general data protection activities, many lump IP address information into this category by default.
The question is whether it truly belongs there.
This post will first examine what, exactly, an IP address contains. Then it will delve into how the U.S., Europe, and Canada have attempted to answer this question. Finally, it will offer some guidance for companies and explain how BlueCat protects IP address data.
What’s in an IP address?
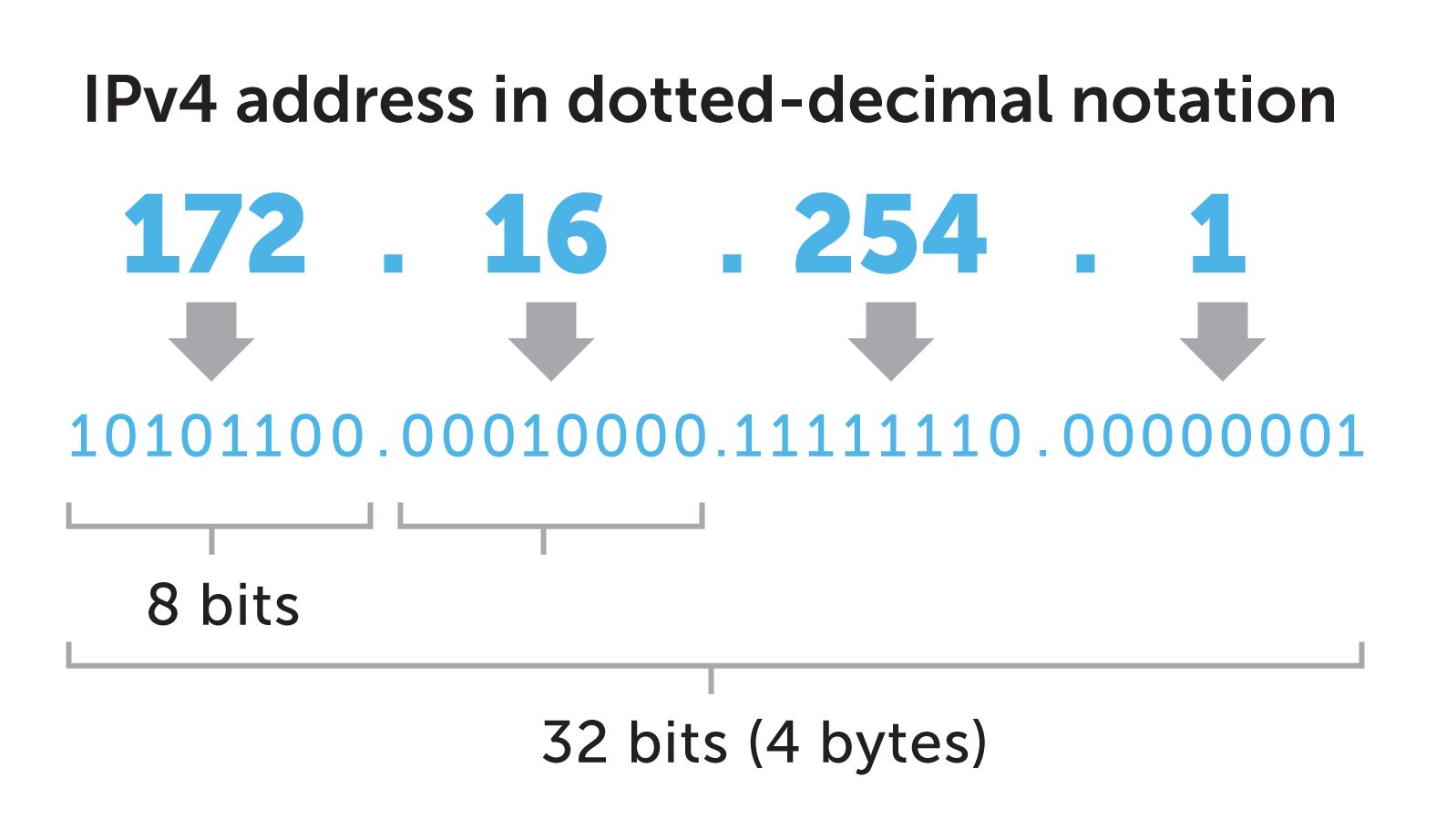
Each device connected to a network requires a unique IP address. The Domain Name System (DNS) translates human-readable domain names (like bluecatnetworks.com) to computer-friendly IP addresses, like 192.0.2.146.
By itself, an IP address merely indicates which device sent a DNS query. This information is not very useful if you don’t know where that computer is and who’s using it. The picture only becomes clearer when correlating it with user logs, query patterns, location data, and other contextual information.
Even then, using proxy servers and VPNs can throw trackers off the scent. DHCP also frequently re-assigns them, known as dynamic IP addressing. That makes it difficult to track a single computer or user over time.
So, does an IP address act as an online identifier or contain your personal information?
U.S. court cases and state laws weigh in: Is an IP address PII?
The U.S. does not have a comprehensive data privacy law. Courts, federal agencies, and state lawmakers have made scattered attempts to address the question.
U.S. courts and federal agencies weigh in
In a 2009 federal district court ruling for Johnson v. Microsoft Corp, the judge declined to provide PII-level protection for IP addresses by themselves. The ruling states that “[in] order for ‘personally identifiable information’ to be personally identifiable, it must identify a person. But an IP address identifies a computer.”
But in 2013, the U.S. Federal Trade Commission revised its Children’s Online Privacy Protection Act Rule to give parents more control over the collection of their children’s personal information. The revision defines personal information to include persistent identifiers, such as an IP address, “that can be used to recognize a user over time and across different websites or online services.”
In 2016, the U.S. Federal Trade Commission Bureau of Consumer Protection offered further guidance in a widely quoted blog post. It said, “We regard data as ‘personally identifiable,’ and thus warranting privacy protections when it can be reasonably linked to a particular person, computer, or device. In many cases, persistent identifiers such as device identifiers, MAC addresses, static IP addresses, or cookies meet this test.”
However, the FTC removed the post from their website. And any substantial guidance from the FTC on the matter disappeared along with it.
Ambiguity in California law, too
At the state level, the California Consumer Privacy Act (CCPA) of 2018 defines personal information to include IP addresses. But only if it “identifies, relates to, describes, is reasonably capable of being associated with, or could reasonably be linked, directly or indirectly, with a particular consumer or household.”
>What the CCPA’s definition of personal information means as a practical matter for businesses is rather unclear, according to the International Association of Privacy Professionals (IAPP).
In February 2020, the California attorney general released draft regulations for the act that could have eliminated some ambiguity. Section 999.302 read: “[I]f a business collects the IP addresses of visitors to its websites but does not link the IP address to any particular consumer or household, and could not reasonably link the IP address with a particular consumer or household, then the IP address would not be ‘personal information.’”
However, according to the IAPP, the next draft regulations published a month later omitted Section 999.302 entirely.
Europe and Canada take a stand on ‘is an IP address PII’
And then there’s the European Union’s General Data Protection Regulation (GDPR). In place since 2018, many consider the GDPR the global paragon of personal privacy protections.
There’s little ambiguity here: The GDPR lists an IP address as personal data.
Under the GDPR, personal data is any information that relates to an identified or identifiable living individual. Further, “different pieces of information, which collected together can lead to the identification of a particular person, also constitute personal data.”
The EU’s Article 29 Working Party, a now-defunct data privacy advisory body for the GDPR, explored this question. The archives of its recommendations note some limited exceptions. For example, IP addresses attributed to a computer in an internet cafe that does not request customer identification.
However, the party noted, “unless the internet service provider is in a position to distinguish with absolute certainty that the data correspond to users that cannot be identified, it will have to treat all IP information as personal data, to be on the safe side.”
What about Canada?
Canada’s Personal Information Protection and Electronic Documents Act, which has been in place since 2000, provides some protection as well. According to the Office of the Privacy Commissioner of Canada, an IP address “can be considered personal information if it can be associated with an identifiable individual.”
In its own privacy policy statement, the Government of Canada considers the IP addresses that it collects to be personal information. This is particularly the case “when combined with other data automatically collected when a visitor requests a web page such as the page or pages visited, date and time of the visit.”
If an IP address is PII, what should companies do?
All of this nuance isn’t very helpful for compliance officers and network administrators.
Many of them default to stricter PII privacy standards for IP address information. It’s easier and the guidance is clearer.
BlueCat strives to protect information while using it in the service of network security software and DNS management. Read BlueCat’s privacy statement for details.
Furthermore, BlueCat’s enterprise-level DNS solution protects IP address information through anonymization, encryption, and restricted forms of access. BlueCat customers can assign a wide variety of controls and restrictions to IP address information. These methods ensure robust data protection regardless of your organization’s view.




