Domain Generation Algorithms in (cyber) threat hunting
Dissecting the malware technique that keeps threat hunters guessing. For cybersecurity professionals and threat hunters, it can feel like advanced persistent threats are always one step ahead.
For cybersecurity professionals and threat hunters, it can feel like advanced persistent threats are always one step ahead – especially in the case of modern domain generation algorithms (DGAs).
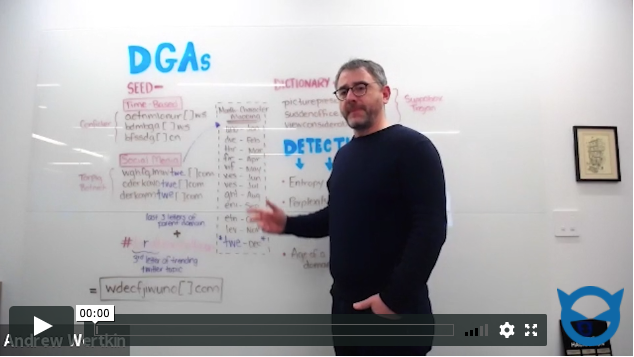
In this whiteboard video, BlueCat’s CTO, Andrew Wertkin, explains:
- How adversaries use DGAs to bury the tracks of communication to Command & Control (C2) servers for botnet malware and ransomware
- How these domains are generated, what they look like, and how they connect to malware
- The patterns your DNS data can reveal to help you weed out and block the malicious domains
Plus, BlueCat Software Development Manager Jeffrey Ip offers more answers on the blog to that what is a DGA question.
