5 holiday tips to make managing DDI a little easier
With the holiday season upon us, here are five tips to make managing your DDI environment a little easier in BlueCat Address Manager.

Key Takeaways
With the holiday season upon us, what better time to present five tips to manage your DDI environment?
Tip 1: Use default domains to create DNS host names from the IP address space
There are many ways to create DNS resource records in the Address Manager user interface:
- Use the Quick Actions from the My IPAM page.
- Create them from the DNS zone level.
- Create them from the IP address level in an IP network.
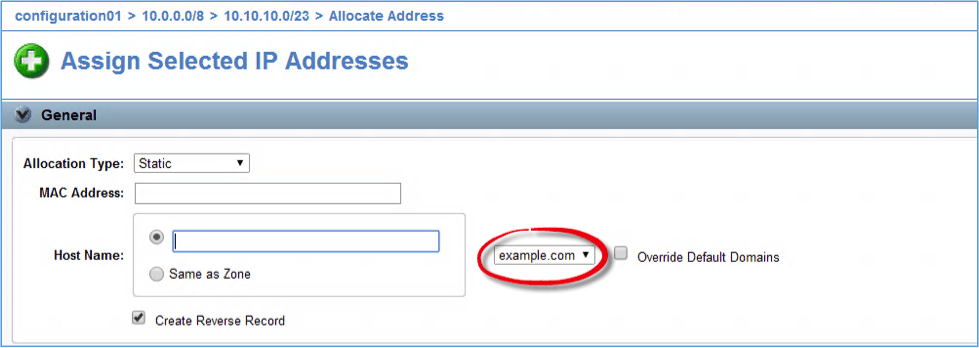
The third method provides an interesting benefit, allowing a user to manage both the IP address space and DNS host records from the same place. The default behavior when creating host records from an IP address is to type the host record’s fully-qualified domain name, such as host1.example.com. While this behavior is reasonable, if you have to create many host records in the same zone, the default domain feature can make administration much easier.
Default domains are set within the IP address space, at an IP block or network level. Wherever you can, create the default domain at the highest block level possible to take advantage of inheritance. Then, when it’s time to create the host record, you simply type the relative portion of the name and leave the default domain name in place. If you need to create a host record with a different domain name, select the Override Default Domains checkbox. You can also create multiple default domains if you use more than one domain name on a regular basis.
Tip 2: What access rights are required to create DNS host records?
While we are on the topic of DNS host names, let’s discuss access rights. Let’s say you want to give a group of users the ability to fully manage the resource records in a particular zone. After granting them the View access right to the configuration so that they can navigate the system, you grant them Full Access at the zone level (which includes all resource records in the zone by virtue of inheritance).
After assigning these access rights, one of the users logs in and attempts to create some resource records. While the user is able to create CNAMES and MX records without a problem, the error message “You do not have access to carry out that action on this entity” appears when the user tries to create a host record:
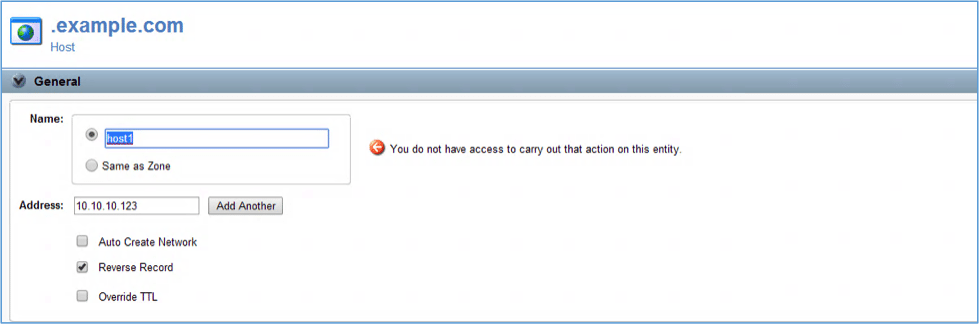
The problem is actually not related to DNS access rights as evidenced by the fact that the user was able to create CNAME and MX records in the zone. The situation is related more to the way Address Manager relates certain objects to each other. In Address Manager, the name portion in a host record is linked to the associated IP address object. If sufficient access rights are not assigned to the IP network, the user cannot create the host records. After assigning a minimum access right of Add to the parent network, the user will be able to create the host records and the problem will be solved.
Tip 3: Remove an intermediate IPv4 block without deleting its child network(s)
You may have encountered the following situation while modeling your IP address space. Let’s say you manage the 192.168.0.0/16 IP address space and you need to delegate administration of a portion of the space, 192.168.1.0/24, to another user. Because you are fairly new to Address Manager, you created both a block and a network representing the 192.168.1.0/24 space. While this appeared to work fine, after some time, you realize that the intermediate block offers no additional value and actually forces the user to click an additional unnecessary object when navigating to the network. You don’t want to delete the /24 block because that will also delete the network. Address Manager includes an IP modeling tool just for this purpose called Merge with Parent.
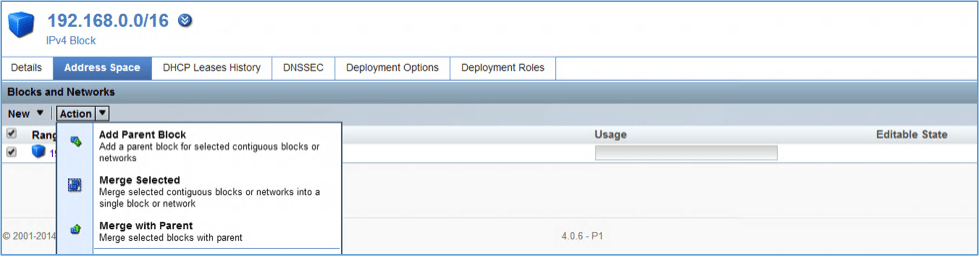
The Merge with Parent tool removes the intermediate block or blocks with the parent without deleting any child objects such as networks or other blocks.
There is one additional important point to be aware of when using this tool. Any deployment roles or deployment options assigned at intermediate IP block level will be passed up to the parent block during the merge operation, unless the same role or option already exists at the parent level. As such, before performing a merge with parent operation, delete any existing roles/options at the intermediate level and then recreate them after the merge.
Tip 4: When resizing a DHCP range, force any existing DHCP clients to get IP addresses from the newly resized range
You may need to resize an existing DHCP range from time-to-time. For example, you decide to implement a new network policy that reserves the first 20 IP addresses in a network for static assignment.(Bonus tip: you can use IP Groups to help manage this.) If your existing DHCP ranges start at an offset of 10 addresses from the beginning of the network, you can resize the DHCP ranges very easily using the Resize tool.
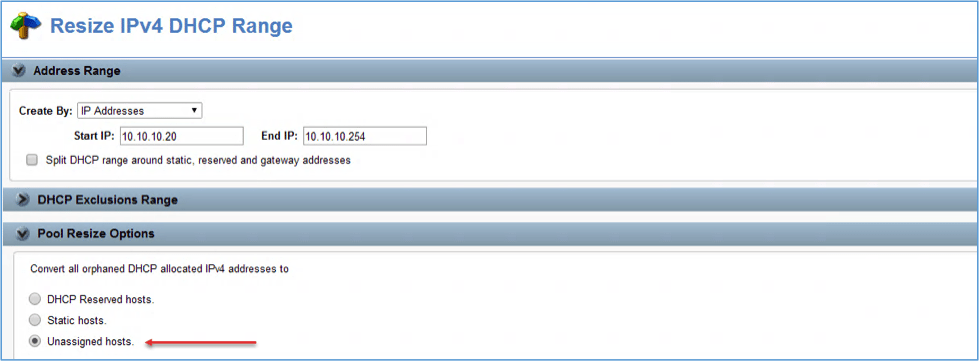
Notice in the picture, when you resize a DHCP range, you must choose from three Pool Resize options. These options apply when a DHCP range is decreased in size and current DHCP clients will become “orphaned”, i.e. their existing leased addresses will no longer be available in the smaller address range.
The default behavior is to have existing DHCP leases converted to DHCP Reserved Hosts (also known as DHCP reservations) when the existing lease expires. If this is not the desired behavior, you can change the settings so that existing leases are changed to static hosts or unassigned hosts. To force clients with existing leases to obtain an IP address from the newly resized range, select the Unassigned Hosts option.
Tip 5: Use Address Manager to manage DNS forest wide zones in Windows
When configuring Address Manager to manage Windows DNS zones, you must create (or use an existing) user account in Windows with sufficient rights to manage DNS. Address Manager uses this account to perform administrative tasks. While this account can be added to an administrator’s group such as Domain Admins, membership in the DNS Admins group is sufficient to manage domain-wide zones. However, if you are managing your organization’s main Active Directory Integrated zone, you will also need to have at least one forest-wide zone, the Active Directory _msdcs_domain.tld subdomain used in certain client queries.
By default, the DNS Admins group does not have permissions to the _msdcs subdomain and if you do not give the group permissions to this zone, an error will result when you try to deploy from Address Manager to a Read-Write server.
To remedy this situation:
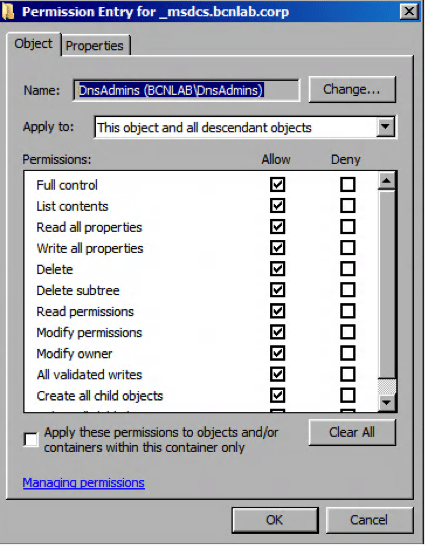
- Open the DNS Manager MMC from a device that can manage the zone.
- Right click the _msdcs_domain.tld subdomain and select the Security tab.
- Assign Full Control permissions to the DNSAdmins group.
- Click the Advanced button, select the DNSAdmins group, click Edit and from the Apply to drop-down list, select This object and all descendant objects.
This will grant the necessary permissions to the zone and all child resource records.