BlueCat’s Declassified Cisco Survival Guide
Heading to Cisco Live? Read our helpful guide to have the best experience possible. While you’re there, come stop by booth #1919 to say hi!

Key Takeaways
So, you’re heading to Cisco Live. That’s great! But before you make your way over there, give this handy guide a read to ensure that you have the best experience possible. Note: These tips are not set in stone (because really, nothing in cybersecurity is). You can modify this guide as much as you’d like until it suits your particular needs.
Tip #1: Be curious
A great way to get the most out of your time at Cisco Live is to keep your eyes open and your ears peeled – there’s lots to see, do and learn. Should you find yourself curious about DNS and its role in security, head over to booth #1919 to learn all about it from some BlueCats. Note: Your curiosity will not hurt these BlueCats, in fact, they thrive upon it. Ask away!
Tip #2: Bring a bag (or some other swag-carrying vehicle)
Something you’ll notice right away is that there’s plenty of neat takeaways from the exhibitors. Balancing a bunch of swag in your arms will take away from your overall experience, so bring something to carry all your cool new stuff in. Not sure where to get started? Booth #1919 is a great option – I hear they’re giving out some pretty awesome stuff.
Tip #3: Don’t forget about DNS security
When fortifying their multilayered cybersecurity strategies, many organizations often forget to secure their network from its foundational layer. That leaves them vulnerable to threats, that then wander freely and undetected across unsuspecting servers, devices, and data centres. Don’t be that person who leaves Cisco Live without visiting booth #1919 to learn how DNS can be used to automatically lock down malicious activity, instantly notify users of suspicious network actions, quarantine patient zero devices, and provide East-West as well as North-South visibility into a network’s data flow.
Tip #4: Stay hydrated
Given that this event is in Orlando (in June), it’s advisable that you drink plenty of water throughout the day. This will ensure that you’re feeling great while you’re visiting booth #1919!
Tip #5: Think about what you REALLY need
While you may be at a Cisco event, there are plenty of options to choose from – there’s no need to have blinders on when you’re walking around the show floor. Cybersecurity solutions like Cisco Umbrella are great, but can be too much for some teams (and budgets). If you’re looking to monitor both external and internal DNS queries, or maybe for an ‘agent-free’ cloud solution, you’ll be pleasantly surprised by what you find when you stop in at booths like #1919.
Tip #6: Head over to booth #1919!
One of the best ways to have a great time while learning something new is by visiting our booth. We’re holding complimentary DNS security workshops, have a 3D threat-spotting game and some handy travel-themed swag. The BlueCats you’ll encounter are very eager to answer all of your cybersecurity questions, so please bring your inquiring mind!
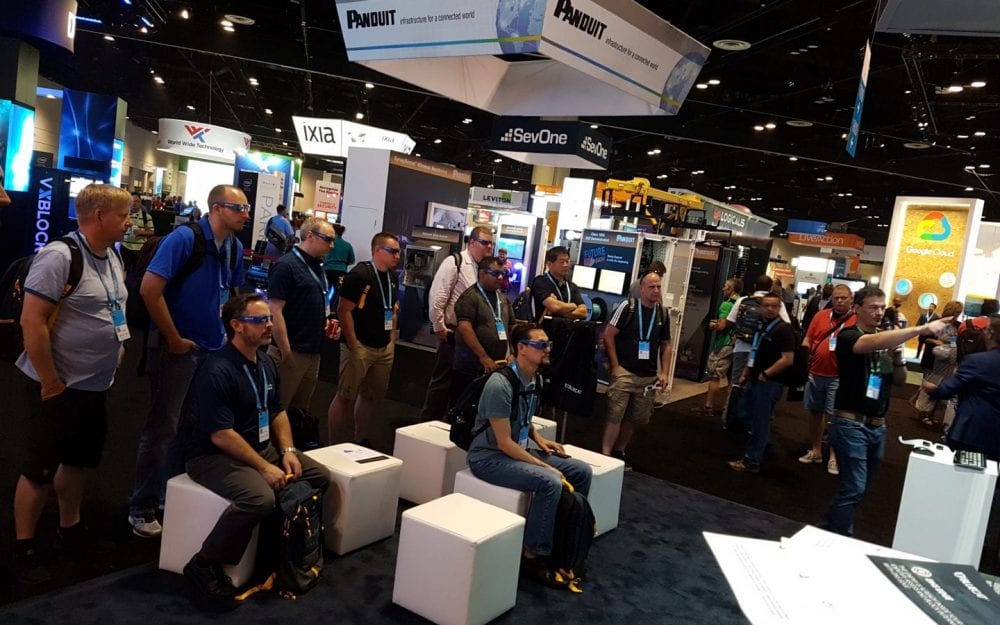
Can you see the threats within? Get comfy, and try it out yourself!
We hope you have a great time at Cisco Live, and that you found this guide to be both practical and helpful. There’s so much to take in and enjoy, so don’t sweat it if you can’t make it to everything on your list – just make sure you don’t miss booth #1919 😉
P.S. That’s booth #1919. See you there!




