Is your DNS being held hostage?
In the second of this three-part series on DNS as a naïve enabler in malicious cyber activity, we introduce persona No. 2, DNS as a hostage.
In the second of this three-part series on DNS as a naïve enabler in malicious cyber activity, we introduce persona No. 2, DNS as a hostage. As a hostage, DNS is recruited as a naïve messenger to route private information over the internet.
The best example of DNS used as a hostage is tunneling. Because DNS is often not monitored, bad actors rely on this to their advantage. As a result, tunneling techniques do not have to be particularly stealthy to leverage DNS. Conceptually, tunneling is like VPN over DNS – a way to tunnel directly through DNS, bypassing firewalls.
First, a short definition of tunneling
According to Techopedia, tunneling moves packets of data across a public network in a way that makes them appear as public information, when in fact they are private. Secure movement allows them to pass through the network unnoticed via a process called encapsulation.
DNS tunneling creates a communication pathway between a client (often malware) and a server to send multiple types of messages back and forth. Two common threats of DNS tunneling are command and control of compromised endpoints and data exfiltration.
Detecting tunneling
How do you know your DNS has been taken hostage and how can tunneling be detected?
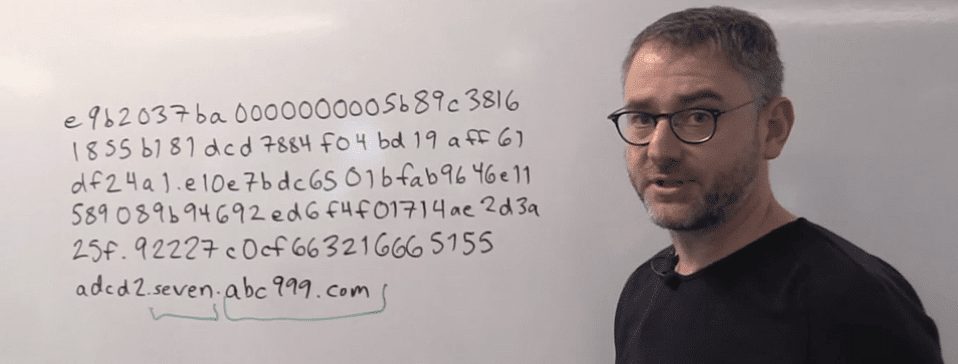
Clues lie in the queries themselves where different patterns are often the giveaway.
There is generally a domain and subdomain evident – then an attempt to put as much data into that host record as possible. Querying for text records, which are not commonly used by a typical client, may be helpful in identifying activity that is attempting to take your DNS hostage.
Important to note is that in tunneling, patterns that include of a series of queries – each different from the next – are common. Each one is unique in order to increase the chances of getting through. These records can be identified by their long string of unique characters, long labels and long hostnames.
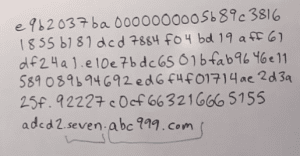
Some may be perfectly valid, using DNS as a mechanism to send messages back and forth; but generally, this is a tip-off that tunneling is underway.
Other patterns are also telling. For example, traffic analysis of the count and frequency of requests.
Patterns that indicate tunneling invariably disclose multiple requests and response pairs over time. Finally, after many, many attempts, a DNS server may respond with a command to execute.
Are queries being sent every minute? This might be a sign of beaconing – bad actors using a network’s self-notification repair strategy for their own mischievous intent.
Traffic analysis also reveals helpful information like volume of DNS traffic, number of hostnames per domain, and domain history. Geographic considerations are another clue. Large amounts of DNS traffic to parts of the world where you don‘t usually do business may also be a tunneling indicator.
Because DNS is not intended for data transfer, it can easily be taken hostage and used as a pathway for malicious communication – and if undetected, can pose significant risk to your enterprise. There are solid clues to follow to determine if your DNS is being held hostage.
The key is to stop it.