Protect Your Network, Protect Your House: Takeaways from the Capital Cybersecurity Summit
On November 14 and 15, the Northern Virginia Technology Council hosted the second annual Capital Cybersecurity Summit in Virginia.
On November 14 and 15, the Northern Virginia Technology Council hosted the second annual Capital Cybersecurity Summit in Virginia. With a number of industry-leading speakers and over 350 attendees, one of the hot topics of discussion included the importance of a well-educated, cybersecurity-savvy workforce in creating a more empowered society.

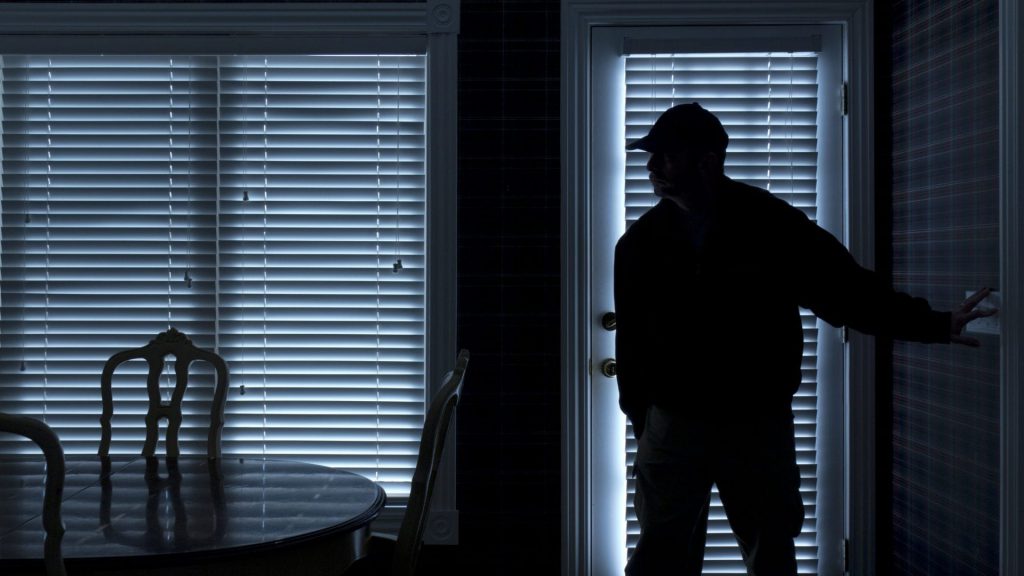
The evolution of hackers, bad actors, malware, and subsequently cybersecurity protocols, inspires an interesting comparison: If you know there is a burglar in your neighbourhood, you wouldn’t think twice to protect your home by any means necessary. And if the burglars changed their tactics, wouldn’t you? Bad actors move fast. You have to move faster. Ignorance is no longer an option. It’s time to educate, prepare, and protect yourself, your network and your data.
Do your cybersecurity protocols prevent burglaries, or home invasions?
Cybersecurity used to be about preventing burglary. The thieves wanted data, and only data – personal information, trade secrets, intellectual property. Once they had it, they usually left the rest of the network untouched.
In today’s landscape, however, cybersecurity protocols should be focused on preventing home invasions. While data remains a valuable target, criminals have discovered that by taking their time, watching patterns, and becoming an intrinsic part of the network themselves, they can gain access to much more valuable assets.
Home invasion-style cyber attacks use your network as a weapon. Criminals are aggregating the computing power of your infrastructure and using it to attack networks in ways you’ve never seen.
DNS is a critical tool for the advanced persistent threats which plague the internet with home invasion-style tactics. Using the naïve characteristics of DNS resolution, bad actors can search for the critical files they want, receive instructions from outside, and develop command and control right under your nose.
91% of cyber attacks utilize DNS, and it’s no wonder – most IT security personnel see it as an uninteresting piece of infrastructure as opposed to a cybersecurity asset.
What can we do to protect ourselves?
DNS filters and firewalls are a step in the right direction, but most are still based on the old burglary model. Out on the network boundary, a DNS firewall can track external network traffic – the simple “north-south” queries. But addressing advanced persistent threats requires insight into internal DNS activity.
Breaches are the new normal, and they rarely happen overnight. In fact, malicious actors are probably on your network right now, searching for the right information or waiting for instructions. In this new home invasion paradigm, the network boundary quickly loses its value – there is no longer any separation between internal and external.
A client-facing DNS security system is like putting a Doberman in every room of your house rather than just one on the front porch. By looking at the source and intent of every DNS query, client-facing DNS security systems can identify even the sneakiest, most patient malware.
By blocking malicious DNS queries at the client level, IT security personnel can prevent lateral, “east-west” movement that allows cyber criminals to maliciously leverage the naïve properties of DNS. As an added bonus, it also protects against suspicious north-south traffic, preventing the “beaconing” behavior which most advanced persistent threats use as a trigger for action.
As advanced persistent threats grow more potent, CISOs need to look for cybersecurity assets wherever they can – even in the most mundane-seeming infrastructure systems. DNS-based security takes cybersecurity to the next level by using this under-appreciated infrastructure as protection against this new breed of home invasion-style attacks.




