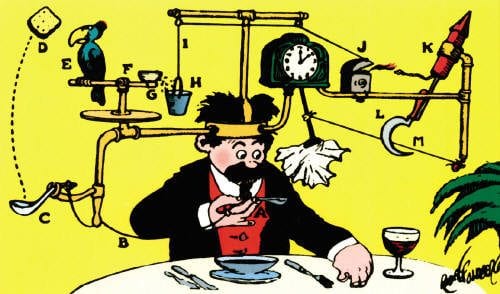
The Risks of Rube Goldberg DNS
“A well-oiled machine.” That’s the highest compliment any network administrator can receive. In a business where people tend to focus on the negative, systems that just work are often under-appreciated.
Key Takeaways
“A well-oiled machine.” That’s the highest compliment any network administrator can receive. In a business where people tend to focus on the negative, systems that just work are often under-appreciated.
When it comes to the Domain Name System (DNS), many network administrators arrive at “well-oiled machine” status by using freely available tools. With spreadsheets to keep track of host names and IP addresses and Microsoft system tools to allocate them, IT staff often feel that anything more to manage and control DNS is overkill – their system works just fine.
Who is Rube Goldberg?
The truth, however, is that these pieced-together DNS management tools are less “well-oiled machines” and more Rube Goldberg machines – a name for convoluted contraptions that fail under simple pressures.
The Architecture
Consider a network architecture which is starting to scale. As the system grows more complex, your IP address spreadsheet and manual management strategy starts to brace under pressure. At a certain point, the probability of human error gets to the point of near-inevitability. A fat fingered IP address inserted into the wrong spreadsheet cell can cause large chunks of the network to fail. Tracing that issue and resolving it can result in significant downtime.
The Administrators
Rube Goldberg DNS is also a personnel issue. When a single person or small group of administrators manage DNS, the entire network depends on their institutional knowledge. Vacations, turnover, or other coverage gaps can turn single points of failure into dramatic consequences. What happens when “that person” – the one who knows how the company’s DNS actually works – decides to leave?
The Security
Then there’s the security issue. In the midst of a cyberattack, spreadsheets and manual tools offer very little to the harried IT administrator. Without a way to monitor and track DNS activity across the enterprise, identifying problems and effectively mitigating their impact in real-time becomes nearly impossible. An astonishingly large proportion of cyberattacks leverage or rely on DNS, yet the Rube Goldberg approach to DNS management offers zero visibility or control when it matters most.
It’s tempting to believe that DNS is basic enough to be handled with basic manual tools, and it may well be true – for a time. Yet sooner or later, any IT staff will face extraordinary pressure on their DNS administration which threatens to expose their “well-oiled machine” for what it really is.
A Rube Goldberg approach to DNS is unsustainable, and it also happens to be unnecessary. With proven tools to properly manage DNS and leverage DNS data for network security, administrators don’t have to live with the risks of a patched together system.
If you’re reading this and realizing your DNS management system may not be such a well-oiled machine, check out our white paper for further insight on common challenges of Microsoft DNS.




