The 3 Types of DNS Security
Cybersecurity professionals are starting to move beyond mere DNSSEC towards leveraging DNS data, as part of a layered protection strategy.

Key Takeaways
Key takeaways
DNS security comes in three flavors:
- DDoS mitigation
- DNS firewalls
- Threat-intelligence
Together, these three layers deliver comprehensive DNS-based security that defends against high-traffic attacks, filters out malicious DNS queries, and leverages threat intelligence to block known malicious domains.
In a previous post we covered the basic differences between DNSSEC (which verifies DNS response legitimacy through cryptography) and DNS security (leveraging DNS data to identify and mitigate threats).
It’s clear that cybersecurity professionals are starting to move beyond mere DNSSEC towards leveraging DNS data as part of a layered protection strategy. In a recent survey, we found that 69% of IT administrators responsible for cybersecurity are concerned about their lack of visibility into DNS data or feel that they don’t have the tools necessary to adequately leverage DNS data for security purposes.
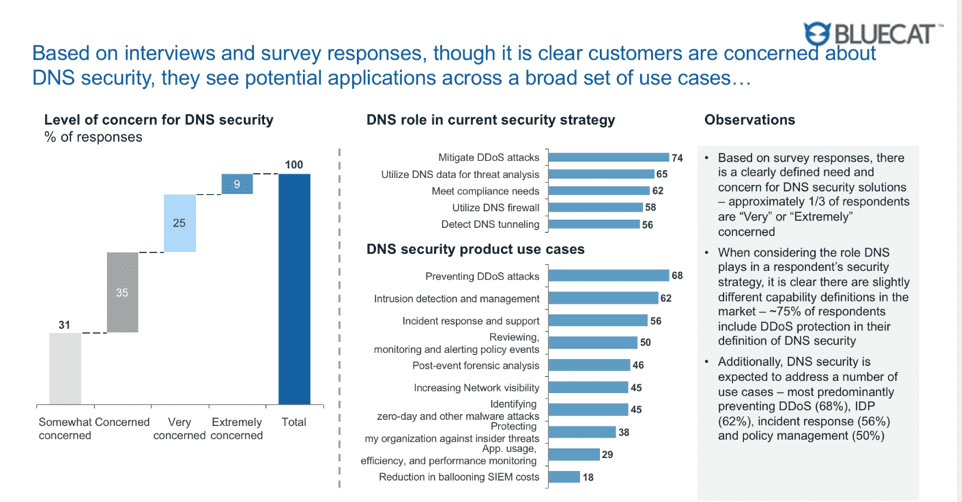
In that same survey, however, we discovered that DNS security is actually a pretty broad category. Cybersecurity professionals know that DNS is important and are concerned about their inability to properly use it, but there was also some disagreement about what DNS security really means.
So how can we distinguish between the different kinds of DNS security? What makes them unique, and how do they apply to today’s network security frameworks?
1. DDoS
The first type of DNS security is deployed in response to a very specific type of threat: distributed denial of service attacks, or DDoS. In a DDoS attack, a server is inundated with DNS responses, often generated by bots or malware from hijacked computers around the world using a spoofed source address, the address of the target, and reflected off of public DNS servers. This tidal wave of DNS responses overwhelms a server’s bandwidth, causing a traffic jam of traffic that prevents normal TCP sessions from getting through – hence the term “denial of service”.
DDoS mitigation is designed to absorb the blow of this type of DNS attack. Usually, that means routing the traffic through a traffic filtering service that has enough bandwidth to handle the load and can strip out the attack traffic, forwarding the normal traffic through to the target server. Compliance standards such as NIST 800-53 provide basic guidance on constructing networks to cope with DDoS attacks; more advanced responses usually involve purchasing DDoS-specific services which provide additional capacity in the event of an attack.
2. Firewalls
DNS firewalls are the second type of DNS security. Where DDoS mitigation dealt mostly with quantitative threats (too many DNS responses), DNS firewalls deal with qualitative threats. In a nutshell, DNS firewalls apply security policies to queries, making a decision about whether each query should be allowed to resolve or not.
If the query meets a defined threat profile, a DNS firewall (usually deployed on the network boundary to intercept outbound traffic) will block the query and respond back with an “nxdomain” to the requesting client. In more sophisticated systems, the DNS query can be sidetracked or “sinkholed” into a security environment where the requested name and source computer can be logged for remediation steps.
3. Threat intelligence
Threat intelligence, the third type of DNS security, takes DNS firewalls to the next level. Where DNS firewalls apply blanket-type protections to query types or other properties, threat intelligence takes a curated feed of known malicious domains and applies it as a security policy through a DNS firewall. Usually these feeds are purchased from third-party vendors and simply “plugged in” to existing DNS firewalls, but it is also possible for users to create their own versions of threat intelligence feeds which customize policies for specific security use cases.
Towards the next generation of DNS security
Seeing the basic forms of DNS security on the market, we knew that something better was possible. That’s why we built BlueCat DNS Edge (Edge), a security tool which goes beyond firewalls and threat intelligence to provide a new form of DNS security. Edge adds new capabilities to the foundation of DNS firewalls and threat intelligence:
- Edge is client-facing. Every other DNS firewall on the market sits on the network boundary, which is great for catching external (“north-south”) traffic but provides no visibility or ability to apply security policies into internal (“east-west”) traffic. However, Edge is able to provide valuable visibility into both, as it’s inside the network – this also brings about richer data.
- Edge sits on the “first hop.” This allows Edge to apply security policies to all traffic, blocking not only malicious queries which are trying to connect with command and control servers on the outside internet, but also malware which is probing within the network in an attempt to discover sensitive information. As well, this assists with a significantly faster response time.
- Edge applies more sophisticated intelligence. Standard DNS security tools use generic policies or threat feeds to apply policies. These provide basic-level protections but often can’t anticipate more sophisticated threat types. DNS Edge was built to identify more complex forms of malicious DNS activity such as DNS tunneling and domain generation algorithms. Using these smarter higher-level policies gives security teams the power to identify and block forms of malicious activity which standard DNS security products usually miss.
So maybe you’re one of those 69% of cybersecurity professionals who want to use DNS security, but need to learn more about the available options. Our DNS Edge page is a great place to start – it’s full of videos, analysis, and ideas for your DNS security project.




