DNS Automation: Internet breakout and SD-WAN domains

Key Takeaways
All the modular layers of today’s corporate networks – clouds, data centers, branch office connections, and SD-WAN controllers – have their role to play in delivering a functional network. Yet navigating applications and services through this jumble of environments can be extremely difficult.
When cloud applications, security services, and other network tools try to connect to the services they need, there usually isn’t a single central network directory which can take them to the right place. Since those services are constantly shifting locations, finding a way to keep connections current is critical to maintaining uptime.
Intelligent forwarding with DNS
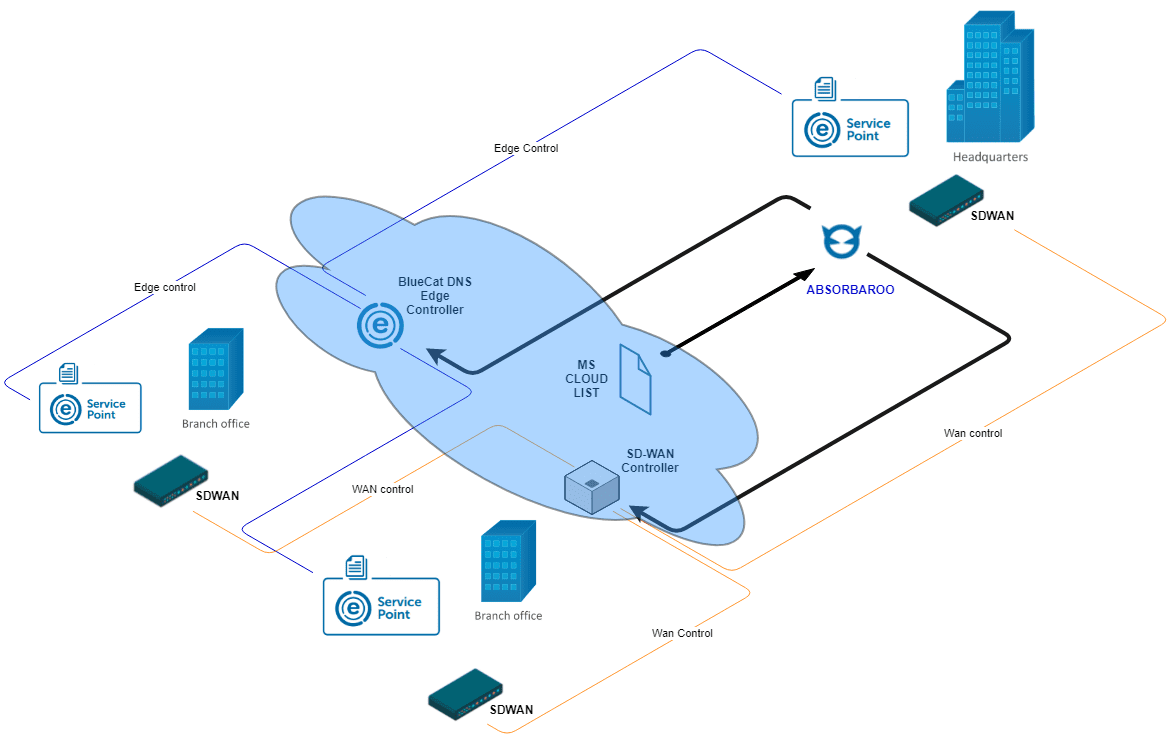
BlueCat’s uniquely designed intelligent forwarding functions can cut through some of this complexity. BlueCat Edge acts as the device facing response layer or “first hop” connection. Network administrators can use BlueCat’s place on the network to optimize internet access to outside services, either through direct connections (an “internet breakout”) or by routing the query back to a home office data center.
This intelligent DNS functionality has a particularly compelling use case for organizations that want to steer service connections away from costly MPLS network backhauls through a local “internet breakout”. This offers a more elegant solution in comparison to the use of deep packet inspection in SD-WAN to direct internet connections.
Administrators can set up routing rules in BlueCat’s platform to resolve directly to trusted external services such as Office 365, Salesforce, or Dropbox. Rules are also available for internal services as well, routing queries either back to a central datacenter or to regional nodes. All of these routing controls coordinate with SD-WAN controllers to resolve trusted traffic directly to service providers.
BlueCat delivers consistent policy across internal and external access points. Using the power of service points, these policies can be deployed anywhere, including the Data Center, Campus, or Branch, to deliver sophisticated LAN side services that facilitate internet breakout.
Keeping track of trusted connections
There is one slight operational hitch which needs to be accounted for. The domains used by cloud services are rarely static. As the underlying IP addresses are updated, load balanced, and taken offline for maintenance, DNS must adjust so queries resolve and SDWAN routes correctly.
To avoid outages and maintain direct connections to trusted cloud services, BlueCat receives automatic updates as the underlying domains are changed. Doing this manually would be a significant headache. Office 365 alone uses over 100 constantly shifting domains. It would also require constant real-time vigilance, as service providers often switch up domains on the fly with little to no advance notice.
Automation to the rescue
Enter Absorbaroo, an automation workflow designed by BlueCat to maintain direct connections to trusted cloud services. Here’s how it works:
- Absorbaroo maintains a constant watch on third party sites for domain change notifications, checking at intervals defined by the network administrator.
- When services post a notification, Absorbaroo downloads the new domain list automatically
- The domain list is pushed through a whitelist into the SDWAN system, updating the resolution data for all of the client devices covered by that BlueCat service point.
- SDWAN sees the resolution on a mutually held white list and allows the connection to be routed directly out to the trusted service.
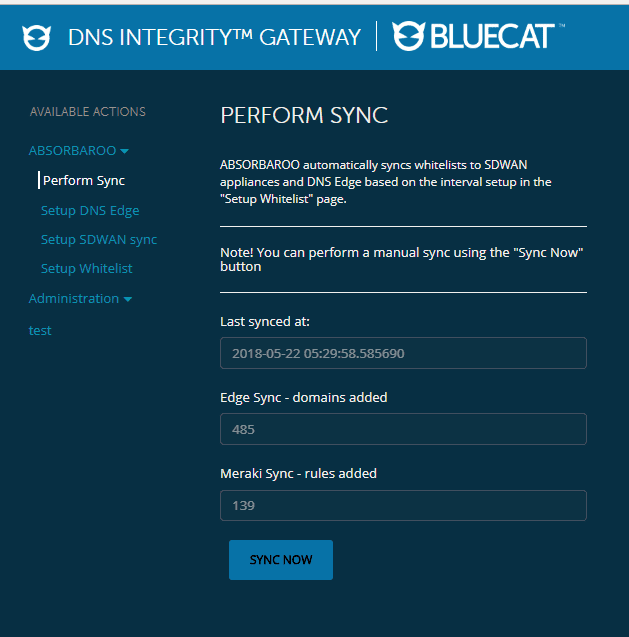
The example workflow posted on our BlueCat Labs GitHub repository uses Office 365 and Cisco Meraki SD-WAN controllers, but the framework can be adjusted for use with any third-party service where internet traffic needs to be managed.
Want to learn more about how BlueCat enables traffic steering? Check out our intelligent DNS video.




