DNS Automation: Host records and selective deployment
Manual addition of host records to DNS can take a lot of time. That’s why BlueCat automated it, saving administrators a ton of time.
Key Takeaways
Adding devices to a network is a basic, day-to-day responsibility of any DNS administrator. New computers, IoT devices, servers, and other equipment are constantly changing the topography of the network, and administrators must assign IP spaces to all of them.
Adding host records is a pain
Mapping these devices onto the network architecture isn’t a difficult task, but it can involve a lot of steps:
- First, the administrator sets up a configuration for the device, assigning permissions and characterizing it in the context of its role in the network.
- The administrator then assigns a top-level domain (TLD) to the device.
- A host or alias record is then added to connect the domain to an IP address.
- The administrator sets an IP address for the host or alias to connect with.
- Finally, the administrator has to validate this entire chain, checking for errors and confirming that the device is operating correctly.
When you’re adding hundreds of devices to the network every day, this process can be a significant drain on administrator resources. There are higher-level, more important things that any DNS administrator could be doing.
Security can also be an issue. To spread out the work associated all those inbound requests, DNS administrators often grant broad access to core systems. This helps with workload, but if one of those outsiders doesn’t follow the proper workflow, they can bring down the entire network.
Automating host records
Gateway – BlueCat’s automation tool for DNS workflows – makes the process of adding host or alias records easier, faster, and more secure.
BlueCat recently published two certified workflows on GitHub which automate host or alias record management. Adding, updating, or deleting these records just got a whole lot easier.
Here’s how it works:
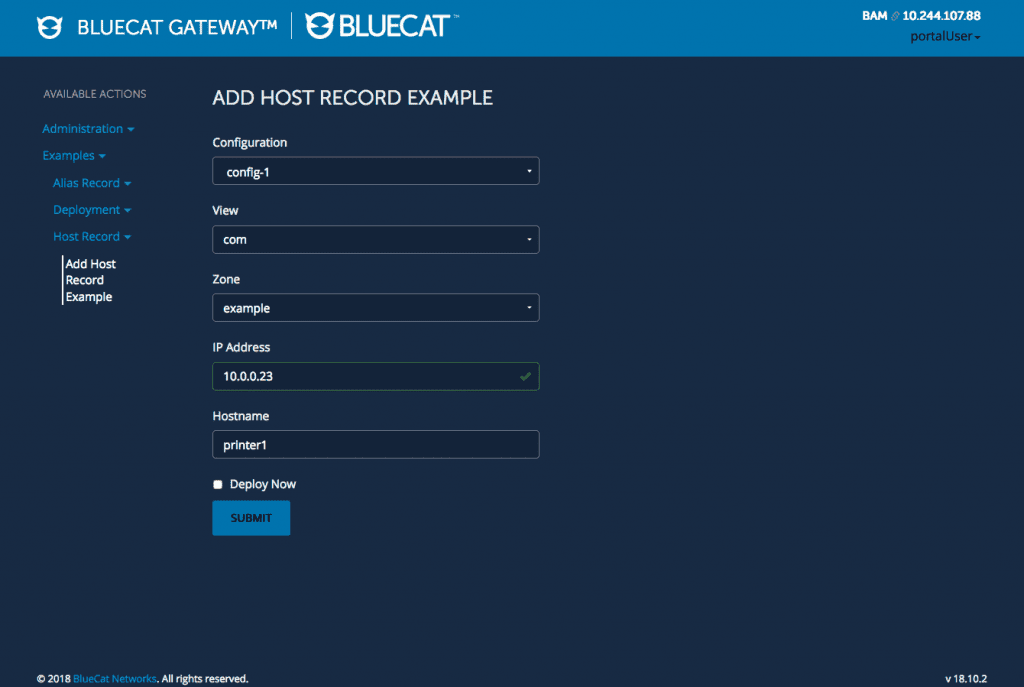
- Administrators set up default configurations for different device types.
- To set up a host or alias record, users select from one of the pre-built configurations in a drop-down menu.
- Users can assign a specific IP address, or the IP address can pre-populate based on the chosen configuration.
- Gateway does all the necessary operational checks automatically on the back end.
That’s it! The whole process couldn’t be easier.
It’s also more secure. This whole process happens through the Gateway UI, which allows administrators to offer pre-built configurations to outside users without granting access to core network infrastructure.
Going Deeper: Selective Deployment
When administrators change anything in their DNS, DHCP, or IPAM architectures, it can take some time for associated records to filter through the entire network. This is a particular problem when a batch of changes is pushed through all at once. This is usually how it happens – administrators will schedule a mass change for a low traffic period and then send out all of their changes.
For various reasons, administrators occasionally want to add just a single device out of that batch rather than the whole thing. Sometimes it’s an immediate configuration fix, sometimes they want to add a single device to the network right away, and sometimes they need to make minor changes on the fly without adding a glut of changes all at once.
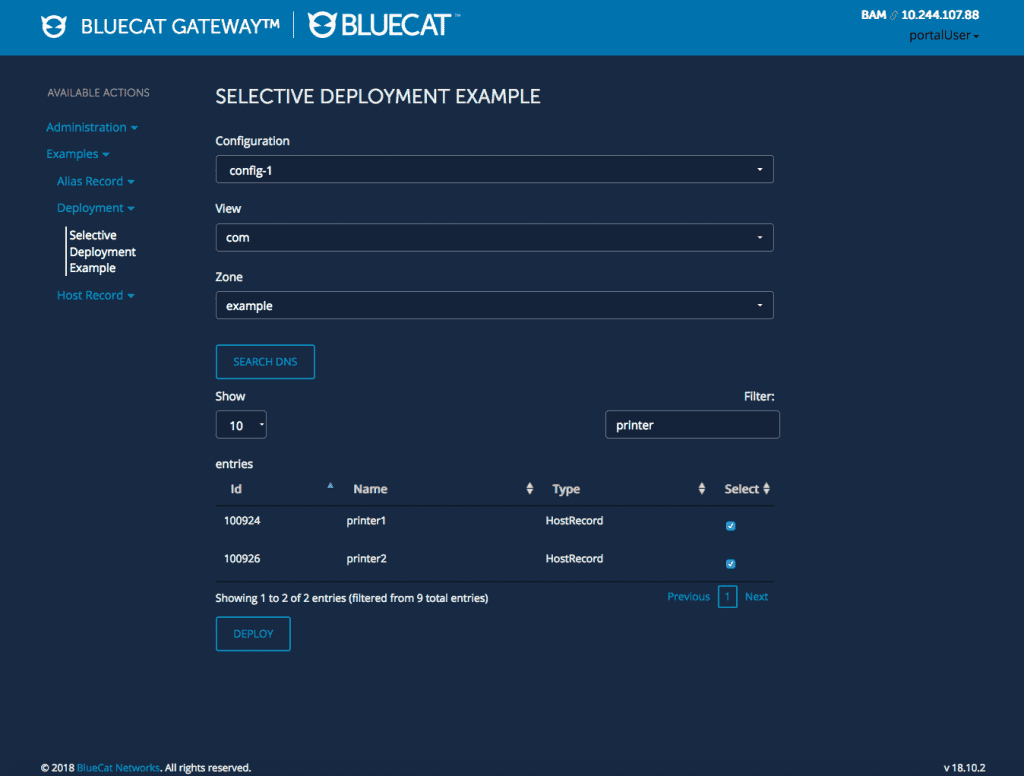
This is where the selective deployment workflow comes in. Using the certified workflow published on GitHub, Gateway users can deploy single changes rather than an entire batch. (Note that this workflow is for DNS only.)
Using the selective deployment workflow is easy. All you do is select the specific change you want to deploy through the Gateway UI, and deploy it. Simple.
Visit the BlueCat Labs GitHub repository for these automation scripts and more.




