IPv4 vs IPv6: What’s the difference?
The transition to IPv6 is here. Learn more with BlueCat about the necessity of it, the timeline, and the numerous benefits and challenges of IPv4 vs IPv6.
Key Takeaways
Everyone knows the internet is moving to IPv6, but when it comes to IPv4 vs IPv6, what’s the difference, really?
IPv4, the fourth version of the internet protocol, is at a crossroads: Its global IP address supply is exhausted. The internet is undergoing a gradual transition to the next version, IPv6. It’s easy to look at IPv4 vs IPv6 as just a difference in numbers. While IPv4 has nearly 4.3 billion addresses for the world to use, IPv6 has 340 undecillion.
But surely the differences go deeper.
This post will examine why the transition from IPv4 to IPv6 is necessary. Then, it will look at progress in the implementation timeline. Finally, it will delve into the specific benefits and challenges of IPv4 vs IPv6.
IPv4 vs IPv6: Do we really need to transition?
IP addressing is a logical means of assigning addresses to devices on a network. Each device connected to the internet or intranet requires a unique IP address.
IP is part of an internet protocol suite, which also includes the transmission control protocol. Together, these two are known as TCP/IP. The internet protocol suite governs rules for packetizing, addressing, transmitting, routing, and receiving data over networks.
The most common format for IPv4 addresses, known as dotted quad or dotted decimal, is x.x.x.x, where each x can be any value between 0 and 255. These values are separated by periods. For example, 192.0.2.146 is a valid IPv4 internet address.
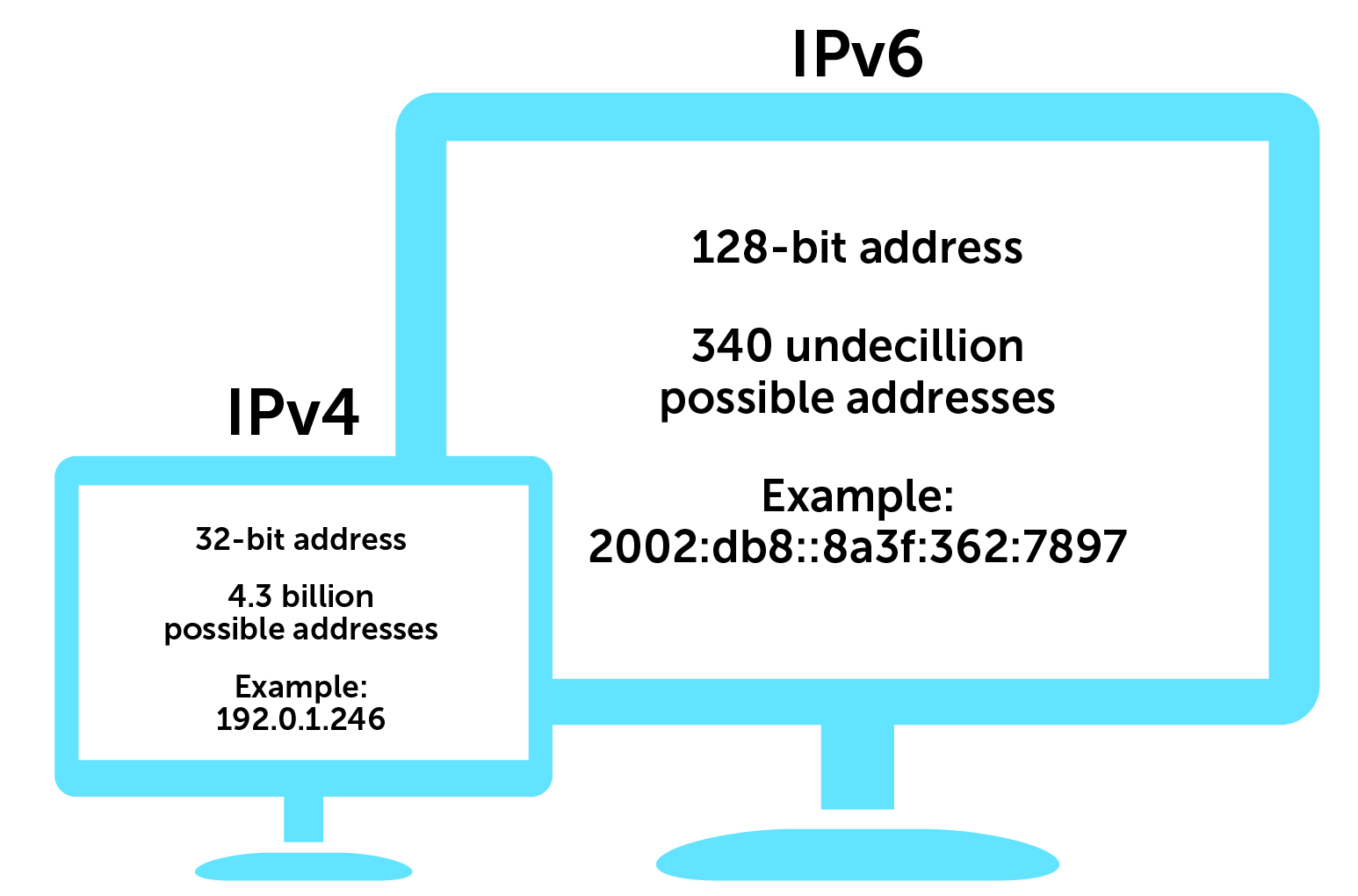
IPv4 is also constrained by a 32-bit address space that limits the number of unique hosts to 232. That equates to nearly 4.3 billion IPv4 addresses.
In 2011, the Internet Assigned Numbers Authority (IANA), the global coordinator of IP addressing, ran out of free IPv4 address space to allocate to regional registries. IANA then recovered additional unused IPv4 address blocks from the regional registries and created a recovered address pool. In 2014, IANA announced that it was redistributing the last addresses in the recovered address pool.
When it’s tapped, there will be no more IPv4 addresses left.
To address this problem, the internet has been undergoing a gradual transition to IPv6. The Internet Engineering Task Force first published the IPv6 protocol in 1998 to eventually replace IPv4’s 32-bit addresses with 128-bit addresses.
IPv6 addresses are written in groups of four hexadecimal digits (using digits 0-9 plus letters A-F) separated by colons (e.g., 2002:db8::8a3f:362:7897).
The necessity of IP address allocation control
Think about it this way: Can you imagine the chaos if someone else also has your phone number? Devices connected to an IP network have the same problem. Every networked device has a unique IP address for good reason. You really don’t want your emails going to the wrong place because the mail server’s IP address was duplicated elsewhere.
While the Domain Name System (DNS) can spot duplicate IPs, the time and effort necessary to constantly sort out issues makes strong allocation control from a sole organizing body mandatory.
How we ran out of IPv4 addresses
On the surface, it sounds as though 4.3 billion unique IPv4 addresses is enough to go around.
However, according to TechJury’s IoT roundup, the average number of connected devices per household in 2020 was 10. This includes phones, printers, computers, tablets, appliances, and Internet of Things (IoT) devices such as smart doorbells and security cameras. Each of these needs a unique IP address.
By this year’s end, the roundup notes, the number of connected devices will hit 46 billion worldwide. That’s over ten times the maximum possible IPv4 addresses.
Furthermore, many IPv4 addresses are reserved for special purposes. About 18 million IPv4 addresses were set aside for private addressing, drawn from a range known as RFC 1918. Most organizations use private addresses on internal networks. Another 270 million are dedicated multicast addresses, used to send messages to many devices simultaneously.
Laying hands on some of the few remaining IPv4 addresses can be expensive. A study on the cost of IPv4 addresses indicated that, in 2020, the price per address from a legal marketplace was $36. (There is an IPv4 black market, too. Crooks con the registries into transferring ownership of IPv4 blocks to them, and then resell them at inflated rates.)
And nobody buys just one. Even if you can purchase a block, there just aren’t enough addresses in the entire IPv4 space for all of the devices that need one.
IPv6 isn’t an option; it’s a necessity.
When are we moving from IPv4 towards IPv6?
The world has been taking steps towards IPv6 for years now, and various organizations are at different stages of IPv6 adoption. At the moment, as far as the average end user is concerned, the two protocol versions peacefully coexist.
In 2012, the Internet Society organized World IPv6 Launch, and has continued to regularly measure global IPv6 deployment. According to its measurements, global IPv6 traffic has grown more than 5000% since, with some networks now reporting 80 or 90% deployment.
That said, there is still a lot more to do.
The U.S. government has directed that 80% of its IP-enabled assets on federal networks must be operating in IPv6-only environments by fiscal year 2025. As of March, the National Institute of Standards and Technology reported that 41% of federal government IPv6-enabled domains were operational. Another 45% are in progress.
For IPv4 vs IPv6, the benefits of transitioning
Besides being the latest version of internet protocol, IPv6 offers several additional benefits that make migration a good idea. IPv4 vs IPv6 offers a significantly larger address space, eliminates complexity, and it’s faster (in theory at least).
Available space in IPv4 vs IPv6
Where IPv4 can provide exactly 4,294,967,296 (232) unique addresses, IPv6 allows for 2128, or about 340 undecillion (3.4 followed by 38 zeroes). While IPv6 addresses could theoretically run out, a computer networking instructor at San Francisco City College did the math. He projected that we can start worrying about exhausting IPv6 in around 9,000,000 AD.
NAT requirements shift
Devices on private local networks using those 18 million IPv4 addresses have no direct path to the public internet. To access the public internet, devices with private addresses require a complex and resource-intensive workaround called network address translation (NAT).
NAT allows enterprise networks to use IP addresses on private local networks internally yet still communicate with the outside world. They can do so via a unique public IP address. A NAT gateway translates the internal address of outgoing traffic to its public IP. And then it directs incoming responses to the appropriate internal system.
One of the benefits of adopting IPv6 is that you get enough addresses to make NAT no longer a functional IPv4 requirement. Every device in most IPv6 environments can have its own IPv6 address without resorting to the private network kludge we’ve been using for so long with IPv4.
Speed
IPv6 makes data transfers more efficient, since devices can directly connect to each other without NAT in the way. These factors make IPv6 faster. (In theory, anyway. Many organizations will still choose to use NAT.)
When it comes to IPv4 vs IPv6, the challenges of transitioning
While there are significant benefits to IPv6, there are some challenges and drawbacks to consider before attempting the transition from IPv4.
Extensive IP planning is both essential and a lot of work
IPv6 is not just a new version of its predecessor. It’s an entirely different ball game.
Migrating a network to IPv6 is a lot of work, and can be resource-intensive. Before transitioning to IPv6, organizations must have a solid IPv6 address plan in place. Otherwise, the chances of a failed rollout are high and IPv6 security risks even more acute.
Every single device needs a new address, and it must be identifiable. That means IT has to know about all of those devices in the first place. That’s not as easy as it sounds with the ballooning number of devices on networks.
Not everything is compatible with IPv6
To complicate matters, not all devices are compatible with IPv6. Application software and networking solutions also may not support IPv6. As a result, testing and validating everything on the network in an IPv6 lab setting is necessary to ensure it can work correctly with the new protocol. IT teams must also make decisions about whether and how to support devices and applications that aren’t compatible.
To aid with compatibility during the transition, many enterprises currently opt for dual-stack implementations. This allows their networks to handle both IPv4 and IPv6 simultaneously. But it can be a tricky challenge to keep it secure and manage how systems choose which connection type to use.
Format and human error rate
IPv6 addresses are more complicated and harder to remember than IPv4 addresses. This can result in a much higher error rate when humans are entering IPv6 addresses in comparison to IPv4. Finding better ways to automate or validate becomes even more important.
All teams that touch the network must undergo training
Network admins, help desk teams, security analysts, and more must shift their mindset and learn the differences between IPv6 and IPv4. Before they can even start using the protocol, teams must know how to effectively design and troubleshoot IPv6 networks. Day-to-day management of IPv6 is different, too. For example, it uses a new set of rules to create subnets and utilizes MAC addresses differently, too.
IPv6 comes with its own set of security considerations
While IPv6 was built to be more secure than IPv4, enterprises must still take security considerations for IPv6 into account. Nothing is invincible. And all new things come with new risks.
The Internet Society suggests several best practices. These include disabling self-generating IP addresses and using allow lists to determine permitted IPv6 addresses for access. Teams must also consider proper network segmentation and methods to block specific traffic to keep cyber attacks (including IPv6 DDos attacks) controlled during remediation.
Furthermore, leveraging stateful DHCPv6 (as opposed to stateless, which requires a much better handle on things like packet capture and packet flow) can ensure better activity tracking, traceability, and visibility.
How BlueCat can help
While the transition to IPv6 is an eventual necessity, it’s not an easy thing to hastily rush into. It’s important to ensure that you have a planned, secure, and tested path for a full and smooth transition. Enterprises must also factor in compliance and mitigating risk for outages and complications. If your organization is considering leaning in, BlueCat’s experts can help.




