Yes, IT should see what developers do in the cloud
Errors and outages occur when admins lack visibility into DNS and IP allocation in the cloud. With Bluecat, central DDI visibility is within reach.

Key Takeaways
Network teams need complete visibility into how a business is allocating DNS and IP space in order to support innovation, optimize network performance, and deliver critical services.
However, when it comes to what’s going on in the cloud, they often have little insight.
Cloud and DevOps teams now have the freedom to innovate fast. But the consequences for core network infrastructure—specifically, DNS, DHCP, and IP address management (together known as DDI)—is often an afterthought. Cloud and DevOps teams use cloud-native or other free DNS services spun up on the fly. And they have little regard for how they fit into the rest of the network. (Spoiler: They don’t, at least not seamlessly.)
This results in network fragmentation, which can be felt by employees and customers alike. It also puts compliance with security standards at risk.
Network teams have decades of experience reading DDI data to gauge network health, optimize resource utilization, and support compliance initiatives. However, visibility challenges related to DDI in the cloud prevent them from doing so.
This post will examine some of the most frequent consequences of poor DDI visibility across platforms in a hybrid cloud environment. It will also explore how BlueCat’s Cloud Discovery and Visibility application can help network teams better support the business as developers race to create applications in the cloud.
This post is part of a blog series exploring some of the challenges network teams experience in the face of enterprise cloud adoption—and how BlueCat can help solve them.
The challenge: Lack of visibility over IP and network utilization
When users rely on applications and services, they just want them to work. It follows that the core DDI infrastructure that supports those applications and services should also work. And it should do so regardless of whether they’re hopping on-premises to cloud, cloud to on-premises, cloud to cloud, within tenants, across tenants, or out to the internet.
Easier said than done. That’s especially true when various cloud vendors and network teams separately manage fragments of the network.
Below are some of the most common networking challenges that BlueCat has observed stemming from poor visibility across the entire network.
Service delays and outages
When DevOps teams stand up infrastructure in the public cloud, under normal circumstances, cloud platforms automatically assign IP addresses to those components. When those IP ranges are already assigned to another part of the on-premises network, a conflict occurs. As hybrid networks are complex, investigating IP overlap in a timely way becomes next to impossible. This causes service delays and outages.
Application failure and latency
When DNS needs to hop across cloud or on-prem boundaries in order to answer a question, it often relies on a complex and brittle set of forwarding rules to do so. Without visibility over this web of connections, it’s easy to make a change and fail to update or create a critical forwarding rule. If you’re lucky, this only causes latency. Often, it leads to application downtime.
Avoidable cloud and operational expenses
Abandoned resources often give clues that they still exist in the form of IP utilization or by sending DNS queries. However, a cloud provider taking care of DDI services abstracts those clues away from even the best-intentioned DevOps teams. This allows services to keep running longer than they need to and drives up costs.
Also, investigating issues without visibility is virtually impossible. As IT spends time or consultant dollars on trying to pinpoint the root cause of a problem, costs rise.
Wasted IP space
Subnet provisioning to cloud teams rarely comes with the responsibility of ensuring efficient utilization of the IP block. In many cases, organizations can end up with the problem of IP space sitting idly, locked in as surplus capacity in one area of the network while another area badly needs the resource. Then, when cloud teams request more IP space, it’s impossible to understand whether they need it or not.
Roadblocks to automation
A lack of centralized DDI data—such as metadata, device data, and IP data—limits an organization’s ability to automate processes. This not only bottlenecks all sorts of innovation but also keeps the business susceptible to costly manual errors. It hampers what and how far they can automate across the enterprise.
Compliance challenges
Many standards, like the U.S. government’s NIST Cybersecurity Framework and Federal Information Security Modernization Act (FISMA), require that an organization can see activity on its network (cloud included) and produce items like DNS logs for auditing and forensics. If cost governance over computing resources is difficult, scrambling to gather a comprehensive repository of DDI data is even harder.
Security risks
Monitoring network activity is essential for securing the enterprise’s data center operations. It’s even more critical in the cloud. That’s because the nature of ephemeral compute and siloed management of cloud environments leaves more opportunity for nefarious activity to go unnoticed. It can wreak havoc on everything from an organization’s operations to reputation.
Compounding complexity
Many of the above problems tempt individual team members to create workarounds, adding complexity to the infrastructure. For instance, in the case of overwhelming forwarding rule sets, an administrator is much more likely to create a new rule as a Band-Aid solution, rather than thoroughly investigate an issue. This adds more complexity and fragility to the infrastructure.

The solution: Centralize DDI data across hybrid-cloud environments
Leveraging DDI data can help track and optimize resource consumption across hybrid cloud environments, support compliance initiatives, and reduce cost. Experts at reading DDI, network teams can apply their knowledge towards helping the business stay fast and resilient when customers need it most. What keeps them from doing so, however, is the challenge of centralizing DDI data across both the cloud and the data center.
How BlueCat can help
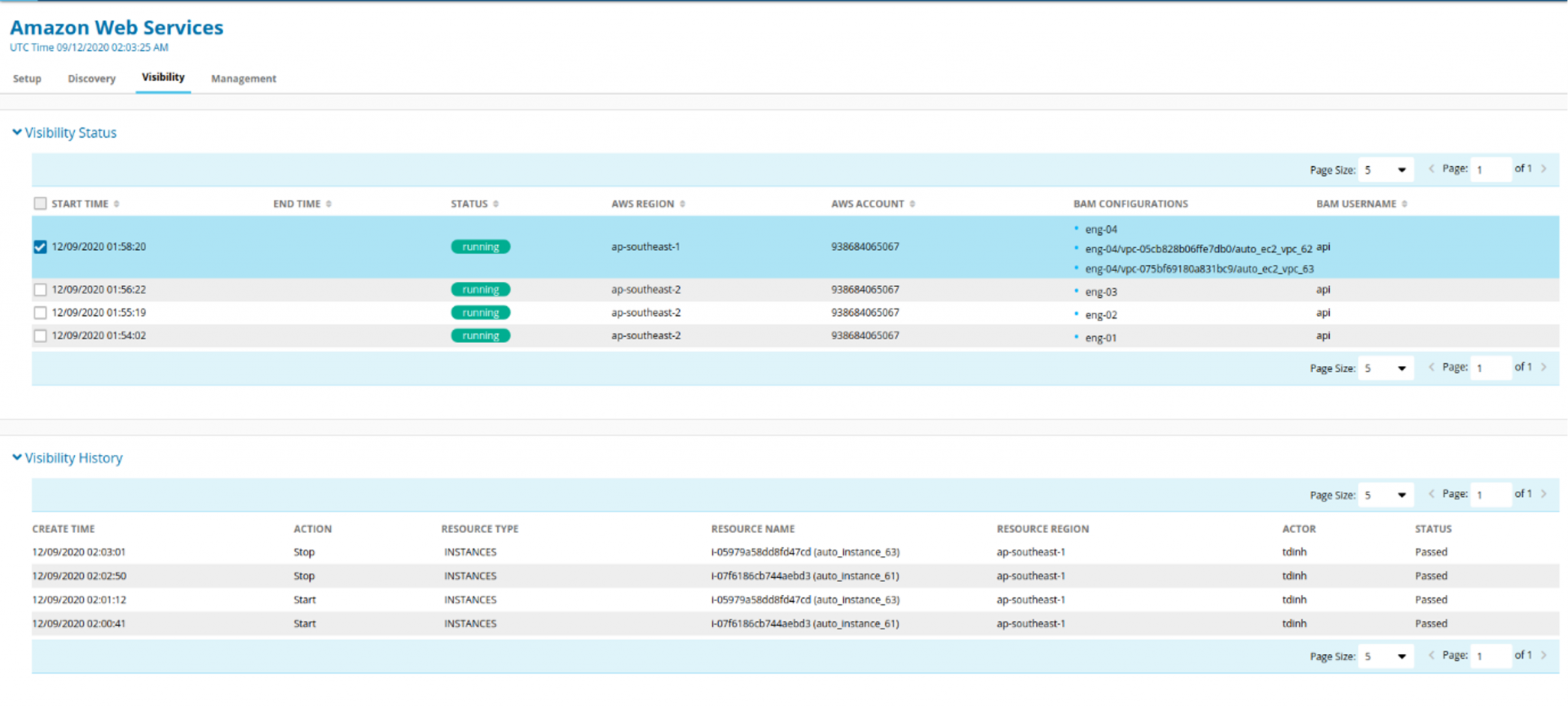
BlueCat Cloud Discovery and Visibility extends DDI visibility into AWS, Azure, and Google Cloud Platform to eliminate outages, keep expenses under control, and accelerate application deployment.
With BlueCat’s solution, network admins can quickly identify, map, and import existing cloud data and infrastructure into a centralized management platform. Once there, admins can view and manage it alongside data from existing networks and data centers.
Furthermore, it provides automated workload discovery, IP addressing, and DNS deployment within existing cloud deployments. Discovery happens dynamically across all cloud platforms. As a result, admins get assurance that they will see other teams’ changes as they manage cloud-based services and infrastructure.
This consistent approach to DNS and IP visibility across the entire network reduces provisioning errors and DNS namespace conflicts.
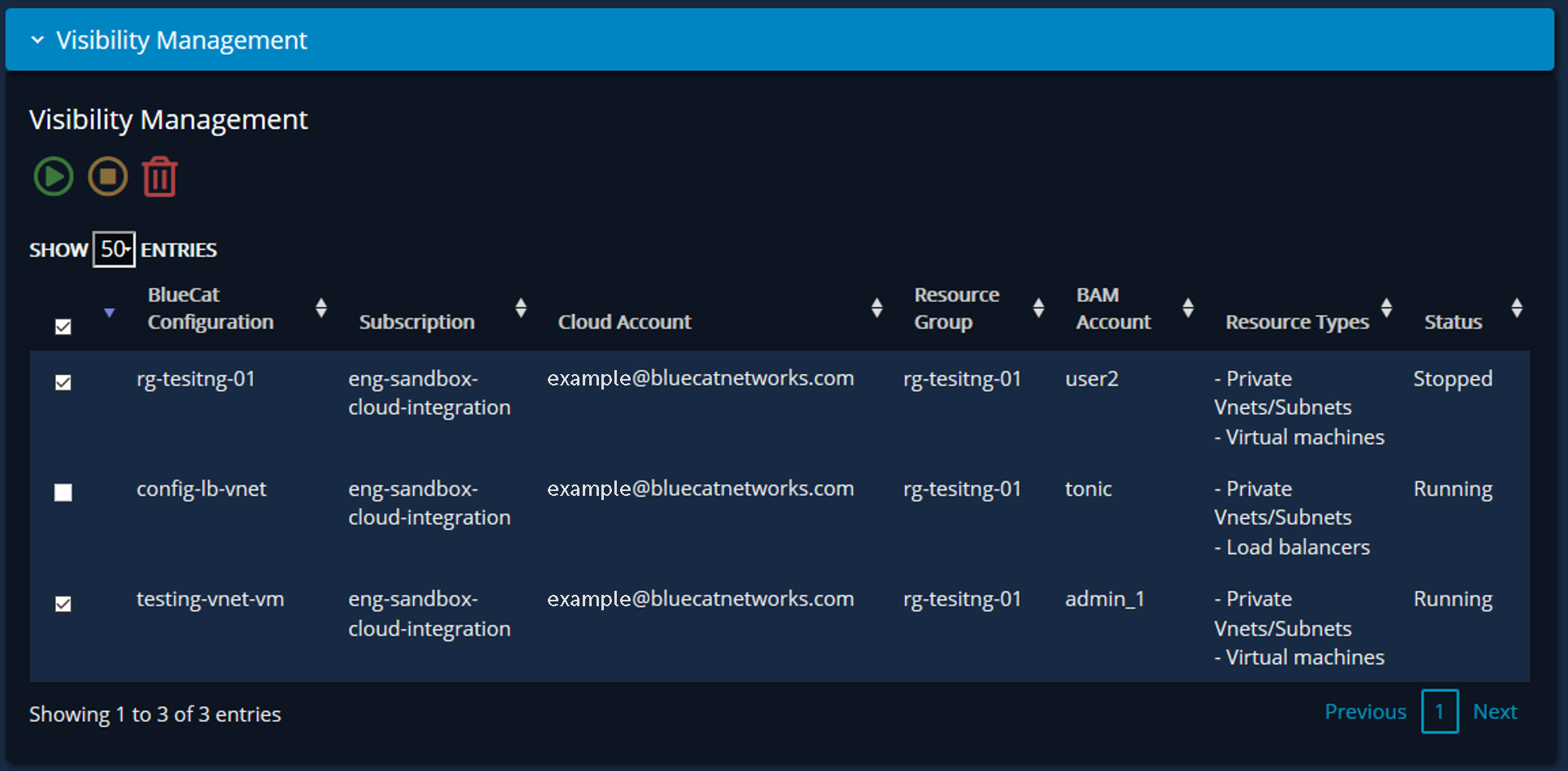
To be sure, dynamic visibility is more than just cloud DNS record assignment. BlueCat also provides visibility into the creation of entire address blocks or networks; private network blocks or subnets in Azure VNet, Amazon VPC, or Google Cloud VPC; workload instances; and related IP addresses and DNS names.
First, discovery at the region level
To start the discovery process, BlueCat Cloud Discovery and Visibility introduces a method to receive cloud infrastructure objects in any region. Following discovery, it is imported into BlueCat’s IPAM solution, Address Manager. Objects can include, for example, IP space, network blocks, and load balancers. Users can create unique target zones aligned to regions containing name resolution DNS records in Address Manager.
Any private address space contained within any discovered private networks (VNet or VPC) is dynamically added to Address Manager. It is represented as network blocks and subnets.
IT teams don’t have to manually create network blocks and subnets. Instead, BlueCat automates dynamic documentation of IP address space in the cloud and on-premises. This gives network admins a single pane of glass for managing all IP space. This even includes space not formally documented but running for extended periods of time.
Next, the discovery of workloads within private networks
Within private networks, any compute discovered is added dynamically to Address Manager as a device instance. These instances hold additional metadata, including machine size, owner, and whether it is started or stopped. When BlueCat adds the device instance, it adds any IP addresses, both public and private, to the infrastructure discovered in the first phase.
Why BlueCat’s cloud visibility solution is unique
BlueCat’s solution dynamically represents cloud compute that is currently running and disassociated from internal corporate DNS domains. It documents DNS records automatically allocated by cloud solutions upon device instance creation as metadata. Most importantly, BlueCat associates domains with corporate naming policy, allowing for easier service discovery by internal resources.
- Creates unique DNS views and zones in its IPAM solution for any public or private hosted zones with cloud DNS services such as Amazon Route 53, Azure DNS, or Google Cloud DNS.
- Documents any IP-based load-balancing devices utilizing cloud-native capabilities as special device instances.
Ultimately, BlueCat ensures that its IPAM platform reflects any cloud-based change to network infrastructure. It doesn’t matter whether it’s the assignment of a single IP address or the creation of entire networks. As a result, application and cloud teams can operate unfettered in hybrid environments. And they can do so while also seeing, and getting out ahead of, potential IP conflicts that pose serious risks to continuity.
Upcoming blog posts will explore each of these hybrid cloud challenges for DDI. And they will highlight the solutions that BlueCat offers to alleviate them. In the meantime, read the Using BlueCat Adaptive DNS in the Cloud whitepaper.




