Cloud DNS: Benefits and obstacles for hybrid networks
Unsure about cloud DNS services and hybrid-cloud enterprises? Learn more with BlueCat, including why it isn’t so simple for managing networks.

Key Takeaways
If you’ve moved parts of your IT infrastructure to the cloud, you might think that public cloud DNS services have you covered.
At first glance, a public cloud DNS service appears like a great option for simplifying your operations. You can let a cloud provider help you manage the complexity of DNS in the environment you already subscribe to. You can bid adieu to your on-premises hosted services.
But is it really that simple?
Maybe if you’re only operating in a single cloud instance (or account, or subscription), sure. But most enterprises don’t. Instead, they work with a hybrid environment of on-premises and cloud or multi-cloud resources.
That’s where its limitations can present real availability, compliance, and security challenges. In short, hybrid environments require some version of centralized management of DNS, DHCP, and IP address management, which cloud DNS does not provide. (Together, these are known as DDI.)
Here’s what’s to come in this post:
- First, it will examine what is meant by a cloud DNS service and how that fits into a hybrid cloud enterprise.
- Next, it will provide an overview of some of the challenges that a hybrid cloud approach presents for managing DDI.
- Finally, it will preview some of the solutions BlueCat offers for more effective hybrid cloud management.
This post is the first in a blog series to explore the challenges for DDI in hybrid cloud environments. Each post will focus on a challenge and how BlueCat helps solve it.
What is cloud DNS?
Traditionally, enterprises have housed their private existing DNS on-premises, either using servers in the data center or hosted elsewhere. This includes both types of DNS servers: recursive resolvers and authoritative nameservers. Typically, these work together in a lookup chain to deliver a DNS answer (such as the IP address of a domain name) to a client device.
Nowadays, many enterprises use software-based solutions to get central visibility into those DNS resolvers and nameservers. This also helps to better manage DDI infrastructure as a whole.
Cloud DNS falls under the Platform as a Service (PaaS) umbrella. Specifically, private cloud DNS provides DNS as a service for compute that runs on the public cloud infrastructure but is inaccessible from public networks.
The three major public cloud providers are Google Cloud Platform, Microsoft Azure, and Amazon Web Services (AWS). They call their services Google Cloud DNS, Azure DNS, and Route 53, respectively. They tout these services as being highly available, global, and scalable.
Following that logic, enterprises can skip using their on-premises DNS servers for applications in the cloud. As a result, managing and accessing DNS for cloud computing becomes easy. (It doesn’t, but that will come in a moment.)
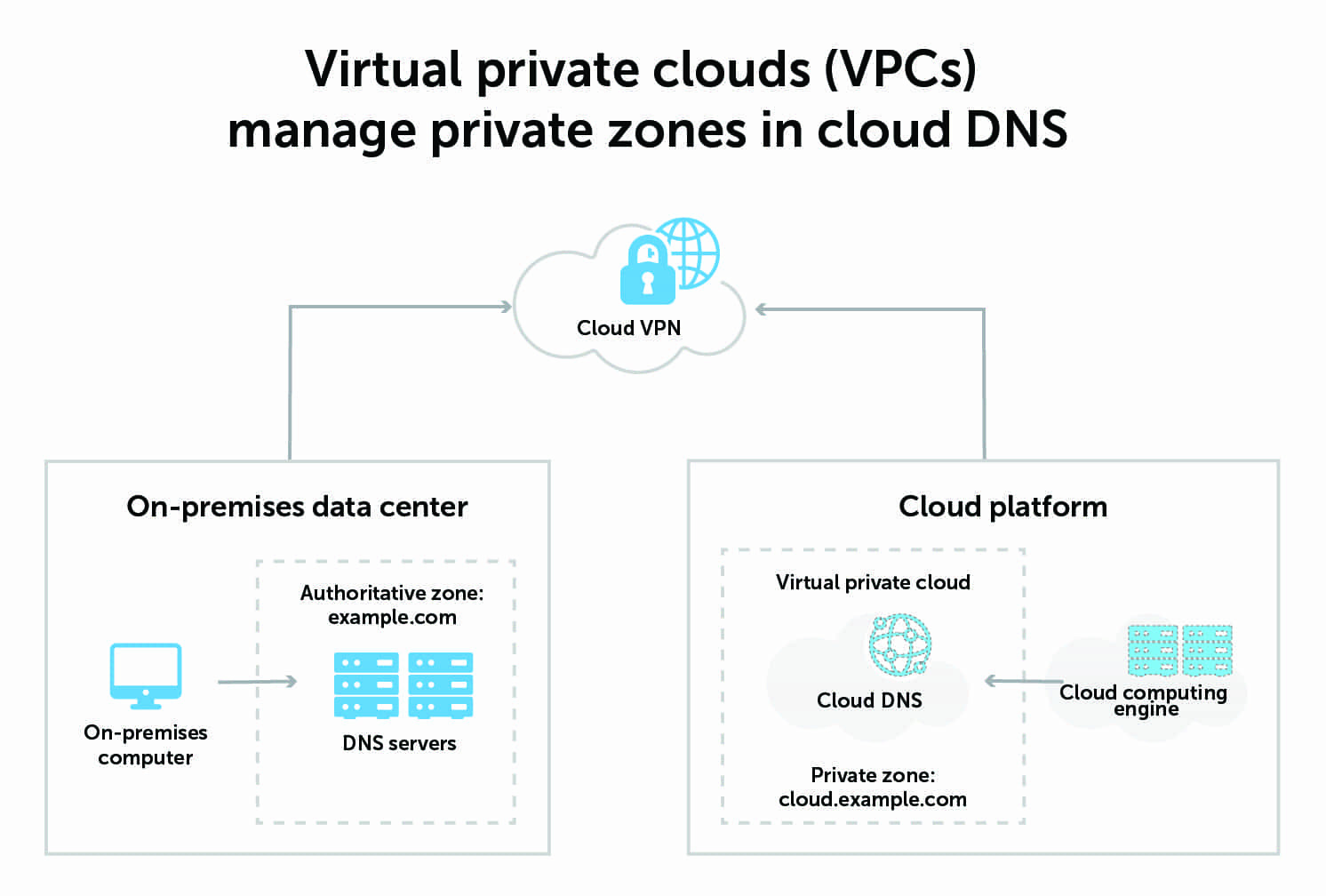
The major public cloud providers have public (internet facing) and private (internal only) DNS authoritative services. Private DNS can be limited to single “accounts” or shared across account and geographic barriers, with limitations. Virtual private clouds (VPCs), also called VPC networks, manage these private zones, which include their own IP address ranges.
Cloud DNS in the context of your inevitable hybrid cloud strategy
Moving to the cloud is happening, yes. It’s finally given DevOps what they need to innovate quickly.
But Rome wasn’t built in a day and neither is a cloud-based enterprise.
Most enterprises have some form of a hybrid cloud approach. In a hybrid-cloud architecture, some applications and infrastructure are in third-party public clouds and some are in private clouds. And some remain in on-premises or hosted data centers. Admins use orchestration tools to manage the workloads and balance between them all.
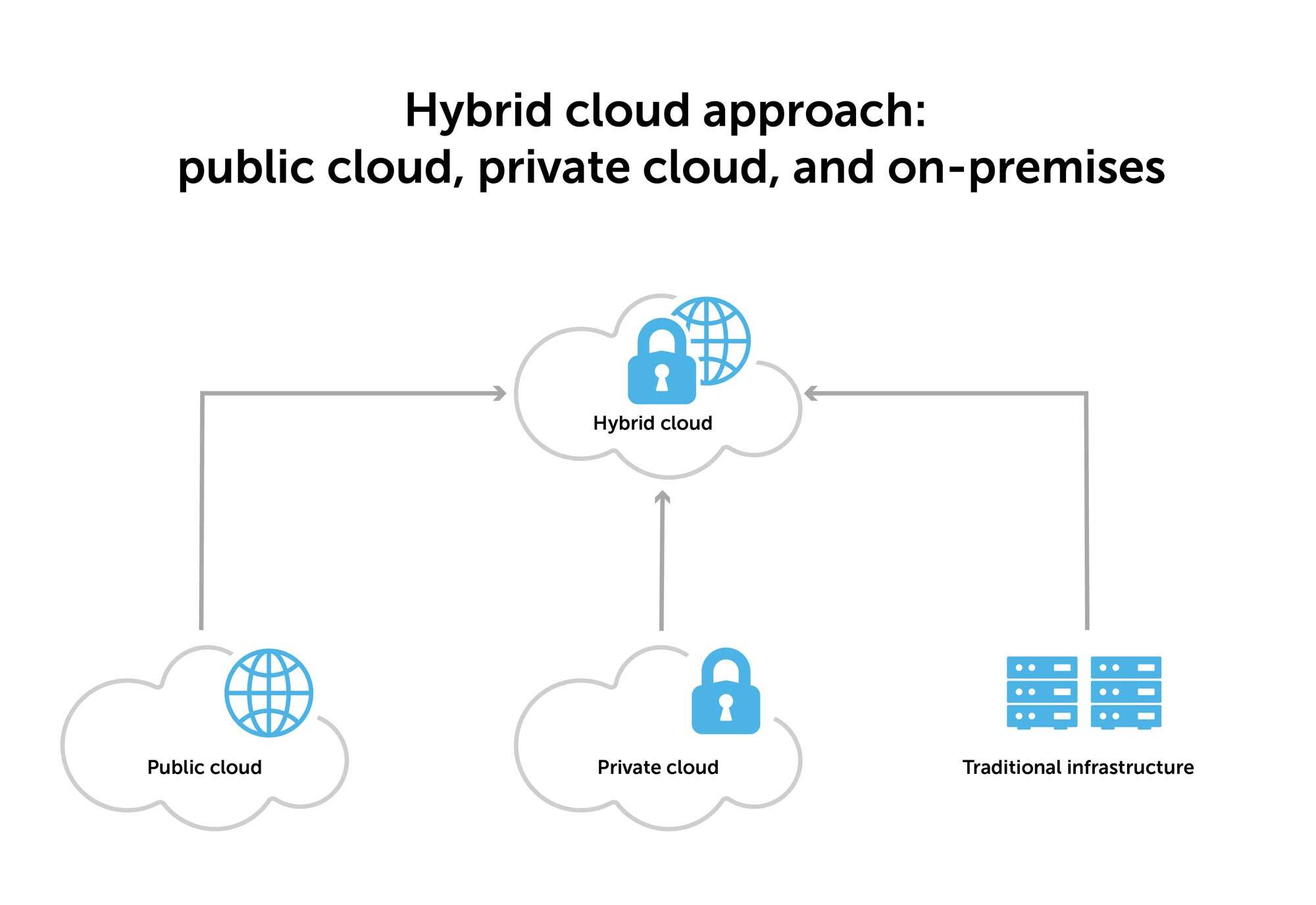
(Multi-cloud means the use of more than one cloud provider for all those cloud applications or components of single applications. An architecture can be both hybrid and multi-cloud.)
The reasons for this approach are numerous. Industries like banking or health care might be prohibited from putting certain types of applications or data in the cloud. Some might be using the hybrid cloud as a way to balance cost or competing demands of stability versus agility. Others still are using it as a stepping stone in their journey to eventually become fully cloud-native.
It’s important to keep in mind that cloud DNS is unlikely to be the only DNS service your enterprise relies on. In unpacking its benefits and drawbacks, you’ll learn that this nuance plays a big role in the value of the service.
Benefits abound
Choosing the cloud for network services offers numerous advantages already built-in. When it comes to DNS, cloud providers reduce the complexity associated with providing DNS services to applications in the cloud. For example, they provide:
- Automatic DNS orchestration: As compute gets provisioned and de-provisioned, DNS resources do, too.
- One-click configuration: Cloud DNS makes it easy to configure DNS based on your routing preferences.
- Load balancing for applications with DNS: Public clouds provide direct integration of their DNS with other deployed components of an application. This automates the process of failover, load balancing, or geographically distributing clients across multiple application instances.
But there are drawbacks, too
Cloud DNS services support applications within their respective public cloud environments. They do not provide the deep capabilities necessary to enable connectivity across heterogeneous environments like the campus, branch, and home office.
Below is a brief list of some of the drawbacks:
- Difficulty connecting resources beyond the cloud (by design). The clouds have different, conflicting, or, in some cases, missing mechanisms to utilize multiple DNS authorities via zone delegation, recursion, or even forwarding. There is no name server interoperability for distributing zone data outside of the cloud-delivered service.
- Difficulty connecting resources beyond the tenant (also by design). Similar to the point above, the clouds have different, conflicting, and inadequate mechanisms to share DNS data across cloud tenants.
- The operational cost of maintenance. Because of how the cloud abstracts complexity, issues that involve cloud DNS are notoriously difficult (read: expensive) to investigate.
- Lack of DNSSEC support. AWS only recently began supporting DNSSEC. And as of the initial publish date of this blog, Google Cloud Platform and Azure still do not.
- Reliance on a third party. With cloud DNS, your network and enterprise applications are reliant on a third party for an essential network component. When (not if) that provider has an outage, the impacts can be substantial.
A networking approach must fill the cloud DNS gaps
Enterprises need highly available network services that can deploy and scale and across heterogeneous architectures, from on-prem to cloud.
To do that, they need a hybrid cloud strategy that recognizes when cloud DNS is not enough for a project. In those cases, on-prem DNS must be extended into the cloud environment to fill the gaps.
In scenarios where this does not happen, BlueCat often sees four key outcomes:
- A lack of visibility into cloud DNS leaves the organization guessing at network and IP space allocation. This leads to data errors, conflicts, and outages.
- Cloud and on-premises DDI are separate entities, preventing centralized control and management of enterprise-wide DDI.
- Complex forwarding rules govern DNS resolution across clouds and data centers, consuming resources and threatening misconfigurations that lead to outages.
- The inability to deliver SaaS-based services in an optimal way impacts end-user experience and increases costs.

BlueCat’s hybrid cloud DNS solutions
When cloud and DevOps teams use cloud DNS, they do so on the fly. They often don’t know what that means for the rest of the network, and they probably don’t care. Their job is to keep moving. Consequently, they’ll default to just taking the cloud DNS services and thinking they’re all set.
Network teams, however, care deeply about how cloud development and adoption interoperates with existing network infrastructure. They’re left dealing with the back-end chaos that results from everything cloud and DevOps teams do. And often without the proper tooling or support to do so across siloed environments.
BlueCat solutions help customers keep up with rapid changes in the cloud while bridging to core DDI infrastructure. When it comes to hybrid DNS, there’s no single architecture that works for everyone. BlueCat’s approach integrates cloud-native tools that cloud teams already leverage alongside traditional DDI solutions. It’s a deploy-anywhere solution: in the cloud, in a data center, or at the network edge.
Specifically, this includes:
- Automated discovery of cloud DNS data, networks, and other resources using BlueCat Cloud Discovery and Visibility.
- BlueCat’s centralized platform for DDI management, including IP, namespace, and DNS records.
- A bevy of network automation and orchestration tools for more efficient operations at scale, like self-service provisioning.
- BlueCat’s Intelligent Forwarding, advanced network services that provide direct internet access and traffic steering.
BlueCat offers visibility and interoperability for using public cloud DNS services where and when customers use them. But it also provides global availability and resilience, facilitates conflict resolution, and assures resolution of DNS queries.
Upcoming blog posts will explore each of these hybrid cloud challenges for DDI. And they will highlight the solutions that BlueCat offers to alleviate them. In the meantime, read the Using BlueCat Adaptive DNS in the Cloud whitepaper.




