Three personas of DNS in cybersecurity
Cyber attackers leverage DNS differently for different outcomes: DNS as a facilitator, hostage, or weapon. How is your DNS being hijacked?
It’s easy to understand why cyber attackers use DNS to do malicious things like spread malware and hobble networks to the point of complete denial of service. With all of your internal network traffic flowing through it, DNS service can give attackers complete control of your network.
DNS a contributor in cyberattacks? Yes.
Let’s recall why DNS was created. Since the inception of the internet, every internet address has been defined as a number. As internet use grew, millions of numerical addresses were in play. Managing the addresses and matching them to their correct destinations became increasingly complex. DNS was the brainchild of Paul Mockapetris, who in 1983, linked names to internet addresses in a dynamic and flexible way — simplifying the process of making internet queries.
DNS architecture persists as a the most helpful handshake between the internet user and their requested destination. At its core, DNS is designed to fulfill connections, making it the perfect, naive accomplice in unwanted network activity.
In the absence of preventative policies on network behavior, or without a DNS security solution in place, DNS will simply do what it was designed to do: make connections. And creative attackers know that there are several ways to leverage DNS.
Three personas of DNS
Depending on the (nefarious) intention, naive DNS is pressed into service differently to achieve different results. DNS, in fact, plays three different roles, or personas, to support destructive cyber behavior.
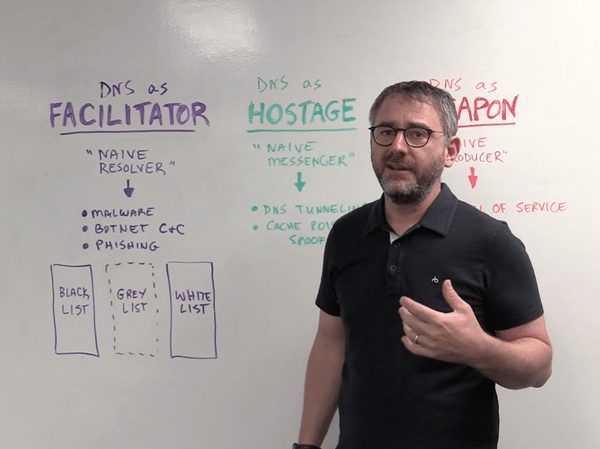
BlueCat Chief Strategy Officer Andrew Wertkin explains the three personas in this three-minute whiteboard session:
- DNS as facilitator
- DNS as hostage
- DNS as weapon
DNS as facilitator
In this scenario, DNS as facilitator, DNS is used as a “naïve resolver”, answering network queries and returning results. DNS goes out to the network, looks up an IP address, and cooperates naively by resolving that request. It acts as facilitator by simply doing its job.
Query results, are of course, compared against Blacklists and Whitelists. Both are known quantities, so confirmed bad actions are blocked, and acceptable ones are given the “all clear”. Things get interesting in the grey area, where queries pop up as aberrations or anomalies, originating from clients or devices that have no business making those calls.
DNS as hostage
As a hostage, DNS in this case is a “naïve messenger”. DNS is used to carry bad messages over the network. DNS tunneling is a good example of this – actually sending data inside DNS requests and responses. As opposed to above, where DNS simply looks up an address and delivers a response, cyber attackers use DNS to send commands, effectively taking DNS hostage.
DNS as weapon
As a weapon, DNS is used as a “naïve producer”, used to attack a third party.
When you hear about an IoT device, like a vending machine, taking down the network across an entire campus, that’s DNS being used a weapon. DNS is a highly distributed system and can generate a tremendous amount of traffic. That overwhelming traffic, a result of DNS being used a weapon, can create a wholesale denial of service.
Because of the role DNS plays across the network, it is also an obvious target for security compromise. If the very backbone of our networks is so easily hijacked, what can be done to make DNS a less naïve facilitator of bad behavior and create more trusted transactions?
The antedote: DNS as defender
The answer to combating DNS use as a weapon lies in DNS data. DNS as defender, a fourth and vitally important persona, provides insights to detect patterns, block questionable queries and identify suspicious actors. Leveraging that goldmine of activity data, and having the ability to act on it by setting policy, would go a long way to making DNS more resilient, and less vulnerable to being used as a facilitator, weapon or hostage.