DDI scenarios that can hurt your hybrid cloud strategy
During Tech Field Day, BlueCat’s Andrew Wertkin whiteboards three scenarios to show how DDI challenges affect your hybrid cloud strategy.

Key Takeaways
Networking is vital to get right in any multi-cloud or hybrid cloud strategy. However, integrating cloud computing with on-premises network infrastructure presents real challenges for DNS management.
When mid-to-large-sized enterprises adopt a multi-cloud or hybrid cloud strategy, BlueCat sees the following four challenges come up in particular for DNS, DHCP, and IP address management (together known as DDI):
- Network teams have no visibility into or control over cloud networks and DNS.
- Cloud and on-premises DDI silos threaten zone conflicts, errors, and outages.
- An inability to automate and orchestrate rapid change slows innovation.
- A growing mess of DNS forwarding rules to manage hybrid resolution creates complexity, consumes resources, and impacts end-user experience.
Unfortunately, these DDI challenges have very real consequences. But they are often difficult for technologists who don’t specialize in DDI to fully grasp, so they go unaddressed by IT leaders.
To help the broader IT industry tackle them, BlueCat’s Chief Strategy Officer Andrew Wertkin unpacked them during a whiteboard session at Tech Field Day 23. To illustrate how these challenges manifest themselves, he explored common scenarios like setting up a VPC (or VNet), the use of a single DNS zone across multiple namespaces, and hybrid cloud DNS routing setups.
If you missed it, this post will cover the highlights. You can also view his entire 28-minute presentation here.
Scenario 1: New VPCs in your hybrid cloud strategy
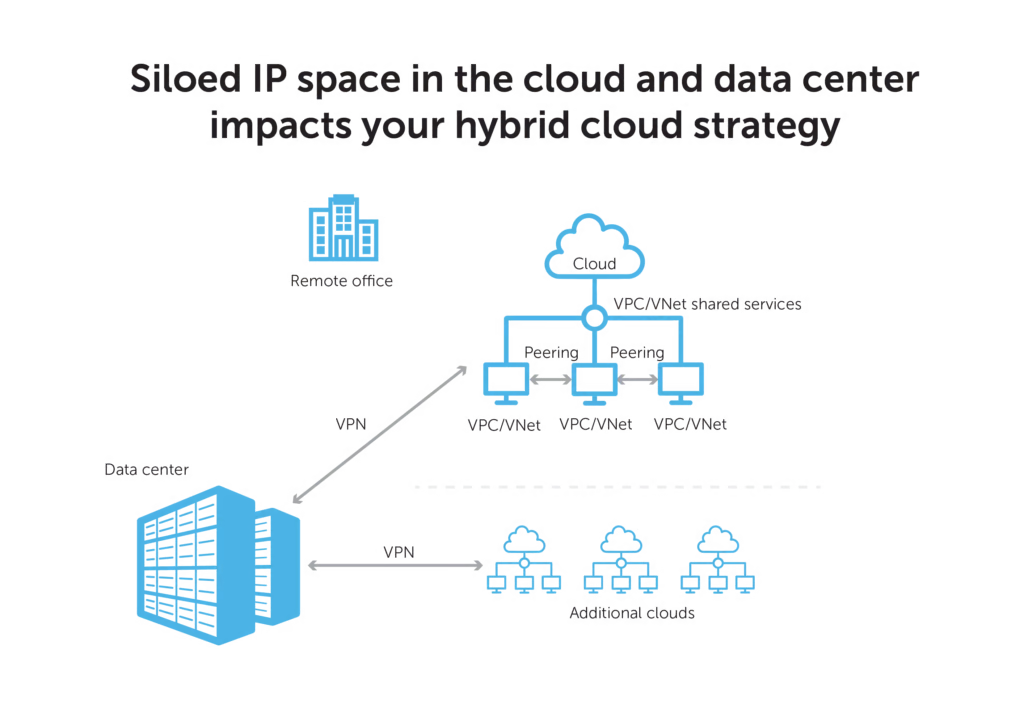
Cloud teams are eager to deploy their applications quickly. Feeling like IT is too slow to give them what they need, they turn to their own form of shadow IT. Teams can create an Amazon Web Services (AWS) or Google Cloud Virtual Private Cloud (VPC) or a Microsoft Azure Virtual Network (VNet) and can provision their own networks and IP space.
The result is private IP space in the cloud, private IP space in the data center, and no connectivity or optimization between them.
Enabling connectivity between these silos is complicated by a number of factors. Each of the public cloud services–AWS, Google Cloud, and Azure–offer customers varying DNS services that make connecting your cloud(s) and your data center difficult. At first blush, DNS services offered by cloud service providers can seem like a cost-effective and simple solution to manage DNS in the environment you already subscribe to. But they prevent centralized DDI management, rendering them not much help for a hybrid cloud strategy.
“We have customers with well over 100 different VPCs that are segmented from each other, per region, per cloud vendor,” Wertkin said. “You end up just with a massive spread of your space.”
This siloed spread has implications for resource optimization, performance, security, compliance, productivity, and more.
On-premises IP planning practices have not yet met their cloud equal
In the on-premises world, long-standing practices—cataloging, documenting, and putting appropriate APIs in place—help network teams plan what IP space should go where and how it should be connected. Such a process is yet to be properly defined and optimized for most enterprises’ hybrid cloud solutions.
In more mature configurations, peering multiple VPCs or VNets together can share data among them. Cloud vendors’ transit gateways make this process easier. But it’s still an entirely unoptimized approach in a hybrid cloud infrastructure.
The shortcomings of the VPN to the hybrid cloud offering
Furthermore, cloud vendors offer the ability to create VPNs to the cloud. While it seems like an easy way to route back and forth between on-premises data centers and cloud network space, it often causes routing problems and performance issues.
Wertkin says he often sees enterprises creating direct VPNs to each cloud. The result might be, for example, two different AWS instances that are close by, but everything is routing back through the data center because they have no ability to route between them.
Those long-standing practices used to plan IP space and routing for on-premises networks are critical for the cloud platform as well, Wertkin suggests. However, they don’t have to be manual. Automation workflows can obtain IP space from your IPAM tool to assign to your VPC or new subnet.
Scenario 2: DNS zones with public and private namespaces in your hybrid cloud strategy
Sometimes DNS zones can have both private and public DNS namespaces. (A DNS zone is the portion of a domain namespace with management delegated to a specific person or entity.)
To ensure that a DNS query resolves appropriately, network teams must ensure that a DNS record is available both internally and externally. These types of double entries are complex but manageable.
Exponential namespace growth
In the world of the cloud, there is suddenly an opportunity for exponential namespace growth. And lots of room for problems along with it.
Some organizations might have one namespace per VPC or VNet, per subscription or account, or per shared services tenant. They might have hundreds of different instances of their cloud DNS. And they might use the same DNS zone across all of them.
“That ends up creating all sorts of complexities,” Wertkin said.“How do I go resolve the records that I need to look up?”
In some cases, they may opt to deploy internal resources in Route 53, which is AWS’ DNS managed service. That also creates all sorts of challenges, because DNS records in Route 53 change.
“All of a sudden, you’ve got this point of fragility. And it seems like a stupid thing to do but it’s done all the time,” Wertkin continued. “Or, they decide to bring up their own DNS server there and start trying to replicate those records. And then something on the inside of the network changes and they can’t access it anymore and there’s downtime.”
With BlueCat’s Intelligent Forwarding, network teams can provision multiple resolution paths across a hybrid cloud environment to simplify DNS operations and improve network performance. Here’s Wertkin’s Intelligent Forwarding demo during Tech Field Day:
‘It gets excruciatingly difficult for them to do their job’
Network administrators work to make sure that every DNS record can resolve a query and resolve it appropriately. And challenges abound when admins are in the dark about what networks might exist in the cloud.
Frequently, when things go awry, it’s not as simple as just a DNS server going down. Instead, somebody’s configured something wrong or a record is missing, which is much more difficult to debug.
“It gets excruciatingly difficult for them to do their job if they don’t have visibility to every hop along the way,” Wertkin said.
Scenario 3: Migrating applications with DNS dependencies in your hybrid cloud strategy
Ultimately, applications are the center of cloud computing. Some are lifted and shifted from the data center. Others might be brand-new, cloud-native ones. Many will need to potentially run across multiple clouds.
Wertkin pointed out that many cloud-native applications and data have a “massive, massive, massive” dependency on DNS for service discovery.
“DNS isn’t just there to look up the DNS record,” he said.
DNS might be crucial to determining a healthy node of a database server or service. Or what container an application needs to communicate with. To some extent, he said, it even acts as a service registry.
However, an application migrated to the cloud might still be dependent on accessing DNS from the datacenter. And now it might be subject to thousands more DNS queries. If each of those queries results in 50 milliseconds of latency, performance will take a hit.
“Whoever wrote the application might just be spamming, pounding on DNS hundreds and hundreds of times a second, if not thousands,” Wertkin said. “And so, we see all sorts of bizarre performance problems.”
Planning to continue your research into ensuring hybrid cloud strategy success? Read how this multinational insurer approached the dilemma of scalable global routing across a hybrid cloud environment.







