How DNS Edge Enables Cloud Innovation without Complication

Key Takeaways
The move to the cloud is fueling innovation, easing development and helping companies provide services to customers or enhance internal capabilities – propelling them ahead of the competition. Cloud is how industry leaders are made.
A common trend in cloud development is microservices. Building in a cloud environment, it becomes easy for development teams to scale and release updates to services most highly in demand while others remain unchanged. A great example of this would be the authentication for a service – used once per session and then its job is done. Another major component – and perhaps the largest component – is the data: how it’s accessed and where it resides. And where it resides is driven by many factors from privacy laws to sensitive data or services – eliminating commercial cloud storage for this data in many instances. This is where locating and accessing the data can be burdensome. Cloud development teams are often not prepared to handle the resulting complications.
Locating data is a job handled by DNS. Cloud developers relying on internal and external domain names to connect to data sources often expect it will just work. But errors often occur, particularly in mixed cases where some data is on-premises in a corporate data center, plus in the cloud environment and even elsewhere. This often involves enlisting network resources to step in and create conditional forwarding and other workarounds so DNS requests by the various microservices can find the data they are searching for. This, however, goes against the nature of the easy deployment, upgrades and scaling afforded by developing in the cloud. Now someone – often unclear who – needs to be dedicated to managing this complication so cloud developers can continue to innovate and produce updates faster and faster. This becomes a DNS problem. But with BlueCat’s DNS Edge™ (Edge), DNS is the solution.
Meeting customers where they already are
Edge is deployed with lightweight, virtual service points that can be deployed in both Azure, AWS, and Google Cloud Platform environments downloadable from their respective marketplaces as of the July 2018 release. In addition to providing visibility and control of all DNS queries, it can enable control of the DNS resolution path. For cloud developers and networking professionals that support them, controlling the resolution path of DNS solves the problems of:
- Hybrid environments where data resides in mixed places inside-and-outside the cloud environment – and often in a corporate datacenter
- Hard to manage conditional forwarding rules
- Cloud environments such as AWS that intend for data to reside within their cloud, thus do not natively support hybrid cloud and on-prem mixes of data sources
With Edge virtual service points deployed within the cloud environment, it’s easy to configure up to multiple namespaces to be referenced for each request in priority order. Consider a consumer-facing e-commerce application that tracks a user’s running history and also sells shoes. Data to support the application is stored in three locations:
- Stored in the cloud: Application data including run history, times, pace and all other metrics collected for the customer;
- Stored in a corporate data center: Customer privacy data and inventory of available shoes and styles;
- Stored elsewhere on the internet: Ads by third-party partners and promotional services.
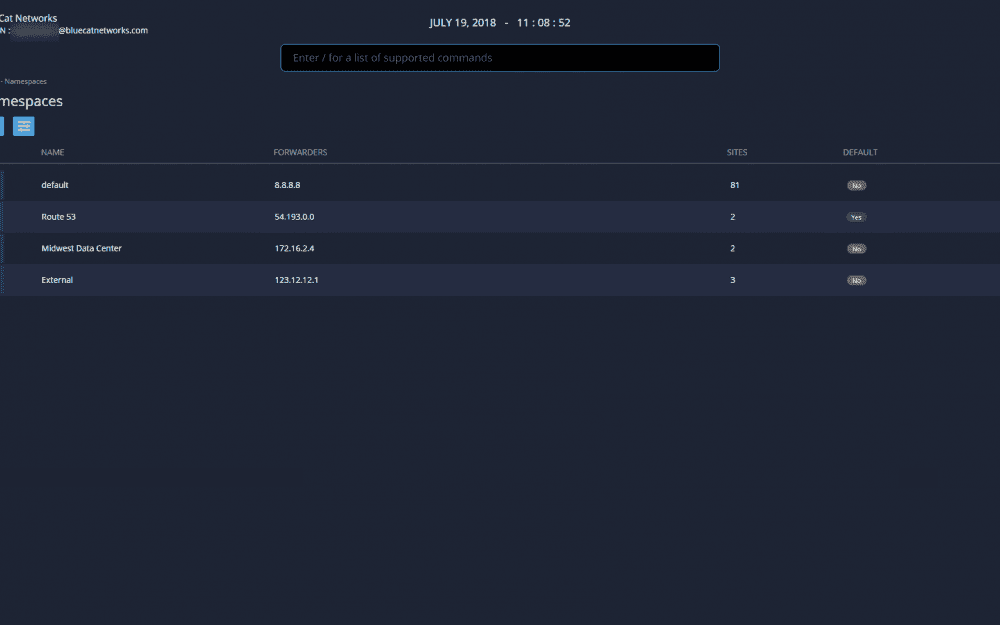
Within Edge, each of these data sources is a DNS namespace. When Edge is configured to be the first hop of the microservices, it’s near effortless to have it check each source in whichever order desired. If the answer isn’t returned from the first namespace, Edge forwards the query to the next namespace in the priority order – this continues until an answer is found.
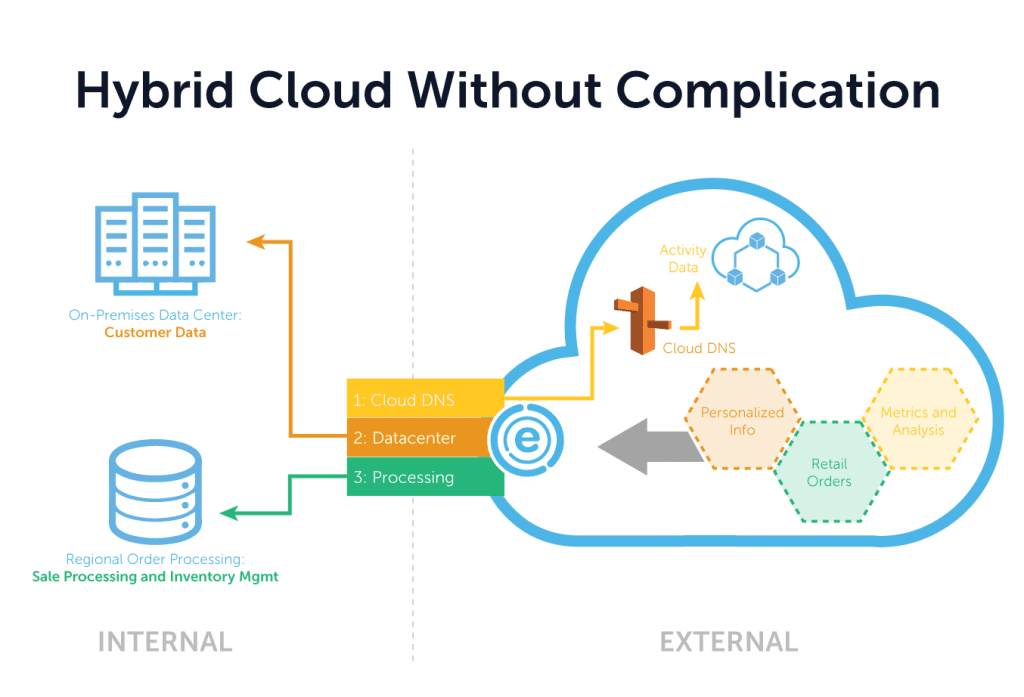
The belief of BlueCat is that DNS should just work – and our customers should decide where their data and services reside. This includes data that’s top-secret or proprietary applications they want to reside within their own data centers. With Edge, we allow this while still enabling cloud developers to build using services afforded by AWS and Azure without wasting time on OS patching, network configurations and more.
But there’s also an additional benefit: visibility and control across the cloud environment. Every DNS query and response is logged in a cloud-managed instance available for review and analysis. Policies can be set to control or limit access to designated sources or from particular microservices. This reduces errors and potential misuse by third parties or malicious adversaries. Smart analytics within Edge analyze all queries to detect patterns of malicious behavior including data exfiltration via tunneling or evasive techniques by cyber attackers such as domain generation algorithms.
Edge makes it possible for cloud development teams to avoid complications and focus on innovating, producing the content or services they want to offer to customers and launch their company beyond the competition.
Learn more about BlueCat DNS in the cloud.





