Know the eight most common DNS record types
There are dozens of DNS record types. Understanding the most common ones can help you detect threats and keep on top of what’s happening on your network.

Key Takeaways
Know thy DNS: A primer on the top eight DNS records
DNS records tell servers precisely how to respond to a DNS query.
There are dozens of record types. And more deeply understanding at least some of them can help you better recognize what’s happening on your network. If you know which record types correspond to which type of activity, you can tell when they’re out of place or being used in the wrong way.
Most importantly, they are a trove of network security gold. Mining your DNS data can help you hunt for threats on your network.
In this post, we’ll provide a quick overview of DNS records. Then, we’ll delve into each of the eight common record types. Finally, we’ll touch on how BlueCat can help you make better sense of all of it.
A quick DNS records overview
DNS (which stands for domain name system) records are officially called resource records. Furthermore, on BlueCat’s platform, we label them as DNS query types. These names are used interchangeably.
There are around 90 different official resource record types. Many of them are now obsolete. Furthermore, DNSSEC, a mechanism that provides authentication and integrity for DNS queries, also uses some specific ones.
DNS servers store records. When a DNS query is sent by a device, that query gets a response from those records with the help of DNS servers and resolvers.
There are eight records that you see again and again: A, AAAA, CNAME, PTR, NS, MX, SOA, and TXT. We’ll focus here on those. Onward!
| DNS Record | Description |
|---|---|
| A | Maps domain names to IPv4 addresses |
| AAAA | Maps domain names to IPv6 addresses |
| CNAME | Redirects a domain to a different domain |
| PTR | Resolves IPv4 or IPv6 addresses to domain names |
| NS | Provides a list of the authoritative name servers responsible for the domain |
| MX | Provides the domain names of mail servers that receive emails on behalf of a domain |
| SOA | Provides important details about a DNS zone; required for every DNS zone |
| TXT | Provides any type of descriptive information in text format |
Common types of DNS records
There are other common types of records that admins and others who occupy the networking sphere may regularly encounter. We’ll delve into those now.
CNAME
A canonical name (CNAME) record redirects a domain to a different domain.
For example, a user enters bluecat.ca in their web browser. Let’s say we own that domain and want to redirect them to bluecatnetworks.com instead. A CNAME record would tell the user’s device, “actually, this is the domain you really want—bluecatnetworks.com.”
To be sure, canonical name records are especially helpful when a single company registers multiple similarly named domains.
PTR
A pointer (PTR) record is the reverse of an A or AAAA record. A PTR record resolves IPv4 or IPv6 addresses to domain names. Reverse DNS lookups use PTR records.
Admins commonly use PTRs for IP addresses on internal enterprise networks. This can make it easy to lookup an IP address to see what domain it maps to on the network.
In addition, a barrage of anomalous PTR activity on the network can indicate performance issues.
NS
A name server (NS) record provides a list of the authoritative DNS servers (also called name servers) responsible for the domain that you’re querying. At the end of the DNS query chain, an authoritative name server is the final arbiter for DNS resource records. Every time a user looks up bluecatnetworks.com, their device will go to our authoritative name server to get the answer, unless the lookup chain has already cached it elsewhere.
Moreover, it’s important to note that NS records point to the domain of the name server—not IP addresses.
MX
A mail exchanger (MX) record stores the domain names of mail servers responsible for receiving emails on behalf of a domain.
These records can be helpful to identify authorized mail servers. An MX record is sometimes called an MX entry, particularly in configuring mail servers.
SOA
Every DNS zone requires a start of authority (SOA) record. RFC 1035 specifies SOA record formats.
The SOA record stores important information about the zone, such as its primary authoritative name server and the administrator’s email address.
Furthermore, SOA records are essential for zone transfers, helping to control the replication of DNS configuration information across multiple DNS servers. SOA records contain a zone’s serial number, which provides a key clue for secondary name servers. If the serial number increases, the secondary name server will assume that the zone has been updated and initiate a zone transfer.
TXT
A text (TXT) record can store any type of descriptive information in text format. For example, network antivirus providers can use TXT records to send and receive information. Furthermore, TXT records often use the sender policy framework (SPF) to publish authorized mail servers. Subsequently, SPF helps prevent spammers from sending emails on behalf of your domain.
Precisely because it can store anything, TXT records can also hide malicious commands. As a result, that can make them attractive to cybercriminals conducting DNS tunneling.
A and AAAA DNS records
Firstly, address (A) records are the most common record type by far. In brief, A records map domain names to IPv4 addresses.
Secondly, as the internet gradually makes the transition to IPv6, there are AAAA records (spoken as “quad A”). An AAAA record is the IPv6 equivalent of an A record, responsible for mapping a domain name to an IPv6 address.
Address records are about the extent of an average end user’s encounter. (Certainly, even encounter is a strong word, as the DNS process happens in the background, unbeknownst to the average internet user.)
Use BlueCat to manage DNS records
The BlueCat platform provides powerful capabilities to monitor and manage your DNS traffic and configurations. Through a single pane of glass interface, you can manage, visualize, organize, filter, and monitor every DNS record query on your enterprise network.
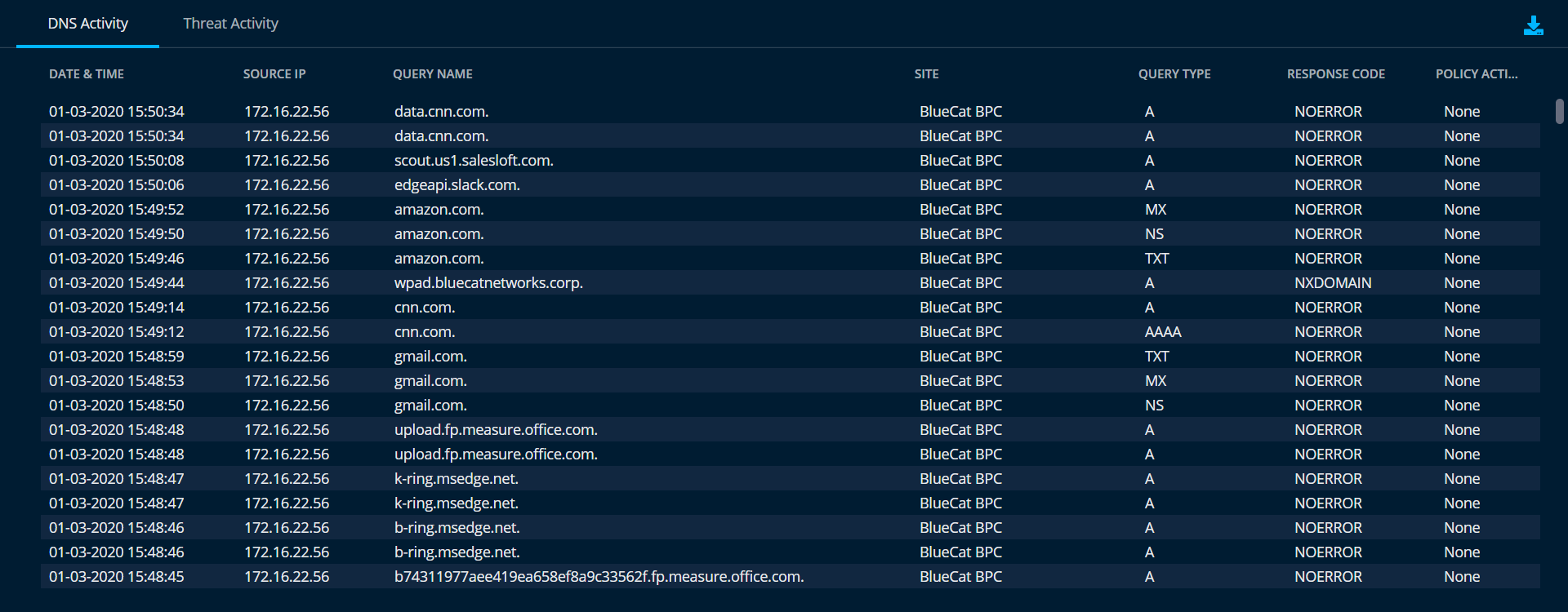
To be sure, with BlueCat’s Intelligent Security platform you can more easily investigate all the intelligence from your DNS traffic to find possible threats lurking on your network. Surprisingly, most enterprises never analyze their DNS data for cyber threats. We like to call it taking a DNS Dumpster dive.




