The enterprise guide to network automation tools
When it comes to automation, the right network automation tools are crucial. Learn what to look for and get insight into what’s available out there.

Key Takeaways
Once you’ve signed up for automating your network, one of your first steps is finding the right network automation tools. With these tools, you can build a framework to transform high-level strategic goals into real operational practices.
You might not have a formal automation practice in place yet. Perhaps you are just looking to start your automation journey as a project in your lab. Even so, you will need to build a toolkit.
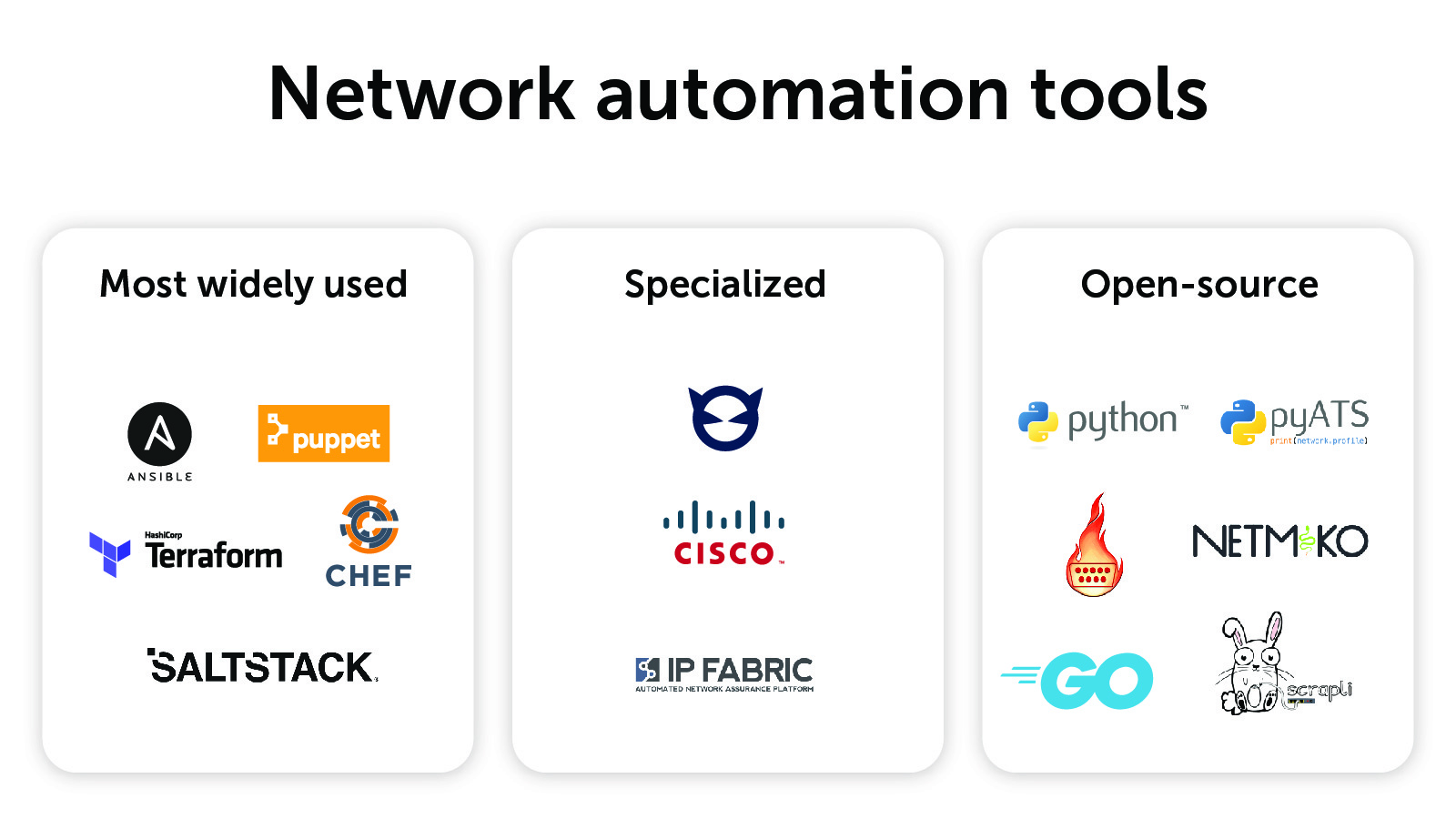
This post will first explore the three things you should look for when choosing network automation tools for your enterprise. Next, it will delve into the details of the five most widely used network automation tools. Finally, it will explore a range of network automation tool offerings in two other categories: specialized, including Cisco-specific ones, and open-source.
It’s important to note that this post is not necessarily meant to recommend the best tools. Instead, it lays out the ever-growing landscape of available solutions. Use this to help inform your decision-making process for selecting the right tools for your enterprise.
How to choose the right network automation tool
The five most widely used network automation tools
Specialized network automation tools
Cisco-specific network automation tools
Open-source network automation tools
How to choose the right network automation tool
Measure twice and cut once! Before you fully commit to one solution or another (or a hybrid of solutions) you should really do your homework. There are three things you should be looking for in your network automation tools:
Alignment with your goals
This might be the most important thing to keep in mind while considering one solution or another. We know automation goes a long way to eliminate human error and drains on IT resources. But beyond that, what kind of automation are you looking for?
Are you looking for network configuration management? Configuration backups? Intent-based automation? Network discovery? Are you looking beyond network operation and want to automate operating systems and applications?
Make a small bullet list of your goals and start with the marketing materials. If the solution does not align or the provider can’t sell you on their ecosystem, move on. Don’t spend time diving deeper into the nuts and bolts of the technical solution.
Technical details
The devil, as they say, is in the details.
What if suddenly you had to deploy a new agent to your infrastructure in order to orchestrate and automate it? Is this feasible in your enterprise? Is the solution Windows-friendly or is it pure Linux? What is the underlying programming language: Python, Ruby, or something domain-specific?
Once you are beyond the marketing materials, you might want to set up a matrix with your narrowed-down selections. You could use a spreadsheet to compare features such as agentless, language, operating systems, etc. Once you have filled it in, you can make an informed decision based on the technical merits of each offering.
Operational maturity
The network engineers and infrastructure staff at your organization were likely hired because of their specialized capabilities. But they may not necessarily have any programming experience.
Asking them to develop fully automated solutions might be like asking them to learn how to play a musical instrument. Some may actually know how to play piano and rise to the challenge. Meanwhile, others will have no idea where to even start.
Keep this in mind while evaluating potential solutions. What is the barrier to entry? How mature is the solution in terms of documentation, industry adoption, and training? How easily can it help classically trained infrastructure staff to adopt a DevOps mindset?
The five most widely used network automation tools
The era of network automation using infrastructure-as-code is upon us. To be sure, the concept has been hanging around for a few years. But the landscape of approaches, tools, and solutions—whether pre-canned or homegrown—has grown exponentially almost overnight.
(My five-year journey with infrastructure as code inspired my eight recommendations for network automation tasks that any network engineer can start with. Note that Step 1 is—no surprise—build your toolkit.)
These infrastructure-as-code solutions try to provide everything you need in one approach, with little reliance on other automation solutions. They are not necessarily incompatible with each other.
That said, it’s rare to see them play together in an enterprise. Usually, it’s when a brownfield solution has to be woven together with a new greenfield initiative, typically after a directional change or migration from one stack to another. (Brownfield solutions must account for and deploy with legacy applications or systems already in situ; a greenfield solution has no legacy constraints.)
Ansible
Ansible has emerged as the de facto network automation tool. It has a low barrier for entry and is easy to use. It also offers agentless and rapid readiness, a large support community, and a wealth of documented examples. Ansible can be used for everything from network infrastructure configuration tasks to Windows and Linux operating system automation.
However, be aware that RedHat has a bit of a complicated ecosystem to adopt. This includes:
- The community-driven Ansible Project;
- The Red-Hat-driven Ansible Engine for IT adoption;
- Ansible Tower, an orchestration, API, role-based access control, and other GUI-driven system; and
- RedHat Automation Platform, a larger one-size-fits-all dashboard with visualizations and insights.
To learn even more about Ansible, you can delve into my list of the 10 best Ansible modules for infrastructure as code that anyone can use.
P.S. You can use the BlueCat Ansible Module for network monitoring, automated configuration, and more on the BlueCat platform.
Chef
Chef specializes in configuration management, defining configurations, and policies as code. Like Ansible, Chef has several offerings. These include:
- Infrastructure Management for configuration management across environments and disparate infrastructure;
- Compliance to maintain and enforce policy;
- App Delivery for application consistency at scale); and
- Desktop for deployment, management, and ongoing compliance of IT resources.
Chef takes its name and brand seriously. It offers a Software Development Kit (SDK) that includes Test Kitchen, Cookstyle, and Foodcritic for automated testing and Chef and Knife command-line interface tools. One of Chef’s strengths is its holistic ecosystem that includes a mature SDK. It allows network engineers to write recipes (code packages) into cookbooks (compiled code).
This SDK is the unique feature that differentiates Chef from Ansible. However, in my opinion, it also requires a bit more operational maturity and programmatic experience.
Puppet
Puppet was one of the first network automation platforms. Like the others, it has its own suite and ecosystem of tools focused on configuration management. It is also an open-source project. Offerings include:
- Enterprise for fast, reliable, and “drama-free” infrastructure delivery and management;
- Remediate to mitigate security risks;
- Comply for policy-driven remediation, enforcement, and compliance;
- Connect for codified automation across teams with self-service; and
- Relay for event-driven automation connected to cloud providers.
Like Ansible, Puppet has its own domain-specific language, Puppet Code, that is used to create desired state configurations. And like Chef, Puppet’s name is very much self-explanatory: We turn our infrastructure into puppets and we are in control of the strings. Desired state can be achieved with Ansible or Chef. But if you are looking for intent-based configuration management, Puppet stands out.
Salt/SaltStack
Salt, often referred to as SaltStack, is a Python, event-driven, open-source network automation and orchestration stack. Salt is also known for its large, friendly, active, and open community. SaltStack was acquired by VMware in 2020. The company is integrating Salt into core VMware capabilities moving forward.
Terraform by HashiCorp
Terraform is rapidly rising as an infrastructure-as-code platform. This is particularly true in the cloud space, where infrastructure is already treated as code. A domain-specific language like Ansible, Terraform uses the HashiCorp Configuration Language (HCL) to concisely describe infrastructure resources.
For BlueCat users, Terraform has providers that allow you to interact with the BlueCat Address Manager. And even the GitHub community is providing Terraform solutions for BlueCat.
Specialized network automation tools
The solutions above cover a broad range of use cases, technologies, and solutions. However, there are specialized tools available for more precise strategic needs, such as DNS automation or infrastructure observability. The good news is that these specialized tools easily integrate with—and definitely compliment—‘the big five’ automation solutions. Given the critical nature of DNS in particular, a specialized automation solution should be considered when launching an infrastructure automation initiative.
BlueCat Gateway
It is worth exploring DNS automation as its own discipline of infrastructure-as-code practices. DNS, DHCP, and IP address management are foundational services. Enterprises are looking more and more at adding quality assurance, reliability, and agility to downstream consumers of these critical services. BlueCat solutions are built with programmability and automation in mind, offering REST APIs, Python libraries, and Ansible modules.
BlueCat Gateway turns business logic into automated workflows orchestrating with adjacent systems. Gateway seemingly integrates with everything, which is pretty remarkable. A notable example is connecting your critical DNS state with northbound APIs.
IP Fabric
There is much more to consider beyond configuration management. This is where IP Fabric comes into the picture, offering automated network assurance. IP Fabric answers the fundamental question, automatically: Is my network healthy?
Cisco-specific network automation tools
Cisco Network Services Orchestrator (NSO)
Simply put, Cisco NSO bridges intent with action. Rich with both northbound and southbound APIs, NSO helps developers connect their automation and orchestration tools to the underlying physical infrastructure.
Cisco Digital Network Architecture (DNA) Center
Cisco DNA is an entirely new Software Defined Networking (SDN) technology. The fabric consists of underlay networks, overlay networks, micro-segmentation, unified wired and wireless experience, and identity-based security. Cisco DNA Center is a network controller and management dashboard that aims to simplify network management using automation and APIs.
Cisco ACI and APIC
Another Cisco SDN offering—this one in the data center—is Application Centric Infrastructure (Cisco ACI). This is centrally managed, using an Application Policy Infrastructure Controller (Cisco APIC). The entire ACI and APIC ecosystem is API-driven and ready-made for automation and orchestration solutions.
Open-source network automation tools
Not all network automation solutions need to be purchased off the shelf. Some are open-source and free!
Python
Network automation, particularly REST API automation, is incredibly easy and accessible with Python. For example, with a few simple libraries, you can automate your own solutions. For example, it can perform create, read, update, and delete (CRUD) activities using requests and JSON data.
P.S. Did you know you can use Python to program automated network monitoring, configuration, and more on the BlueCat platform? BlueCat Labs on GitHub has several Python-based workflows.
pyATS framework
Cisco has an open-source Pythonic test framework called pyATS. Developers can use it to create Boolean-based tests against the network state. These tests are easily written and can be used to test everything. This ranges from cyclic redundancy check errors to Open Shortest Path First or Border Gateway Protocol neighbor states.
The pyATS framework includes the actual libraries called and used to perform your tests.
These libraries are Pythonic device.learn() or device.parse() functions used to gather network state. Device.config() can be used to push configuration.
Netmiko
Netmiko is billed specifically as Python for network engineers. It aims to simplify Paramiko and the SSH connection utility. Netmiko also offers a multi-vendor network automation solution. You can also find Netmiko on GitHub.
NAPALM
NAPALM (Network Automation and Programmability Abstraction Layer with Multivendor support) is a Python library. It provides a standard API to any number of network devices, including Arista, Juniper, and Cisco. You can also find NAPALM on GitHub.
Go
Go is another open-source programming language for building software that is simple, reliable, and efficient. The major difference from Python is that Go builds compiled code. This eliminates the need for the user to import all of the required libraries to run the code. And it makes it very attractive to network automation developers.
Scrapli
Scrapli, available on GitHub, is an open-source community project from Carl Montanari that provides Python screen scraping for network devices. This is incredibly handy if you want to create your own customized parser.
Ultimately, automating your network is a marathon, not a sprint. It’s a long-time journey without a finite endpoint. If you are just starting out, I recommend you take as much time as your enterprise requires. Pick the network automation tools that fit your culture and existing practices as much as they fit your technological skillset.




